4
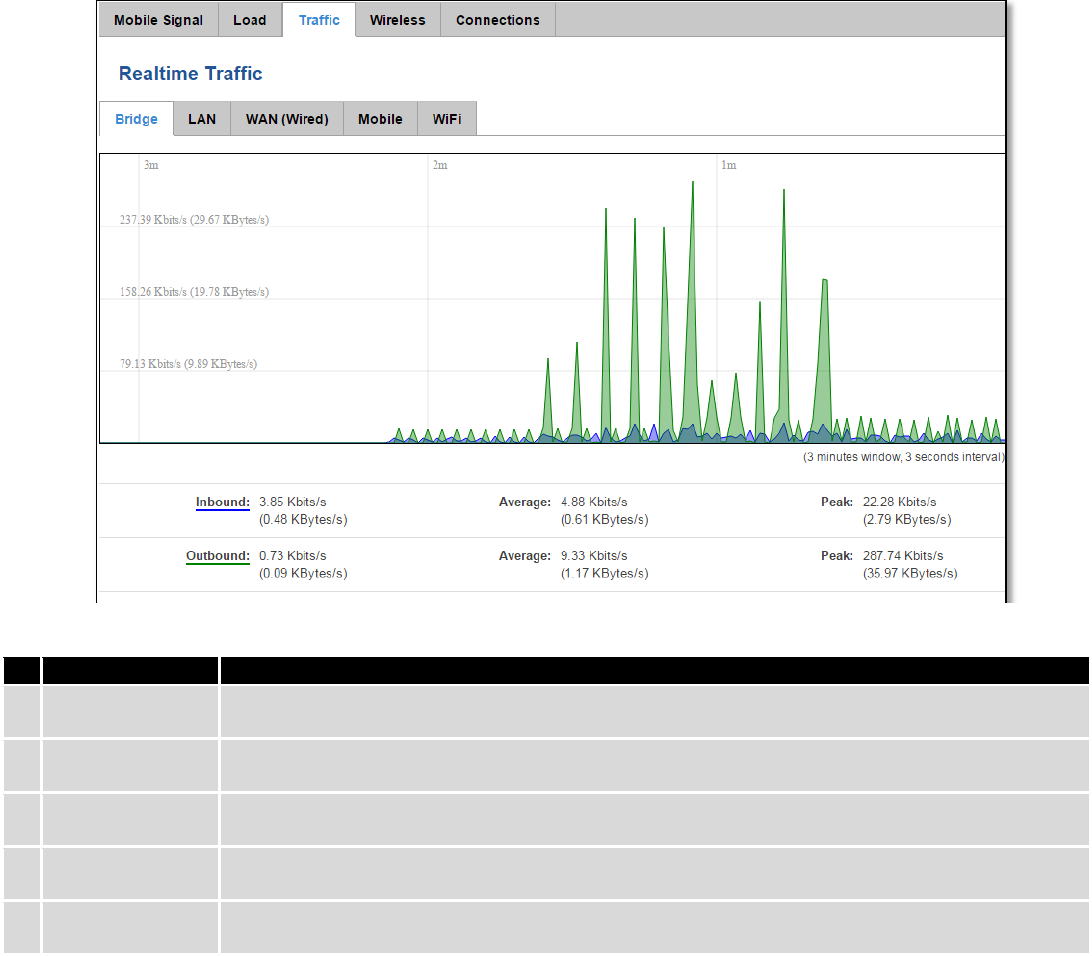
6.7.3 Realtime Traffic ................................................................................................................................ 35
6.7.4 Realtime Wireless ............................................................................................................................ 36
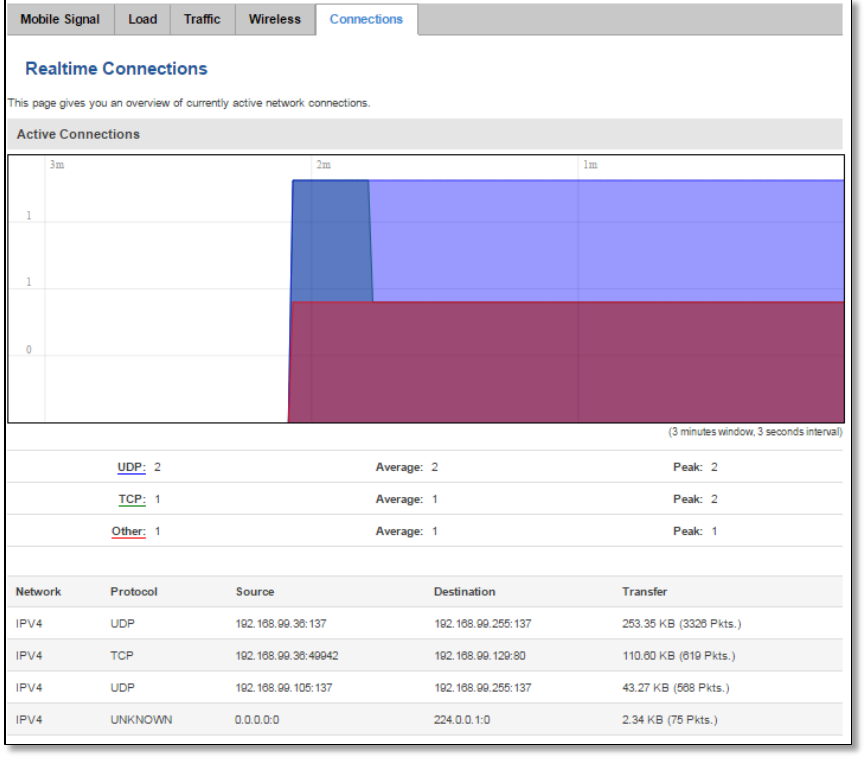
6.7.5 Realtime Connections ...................................................................................................................... 37
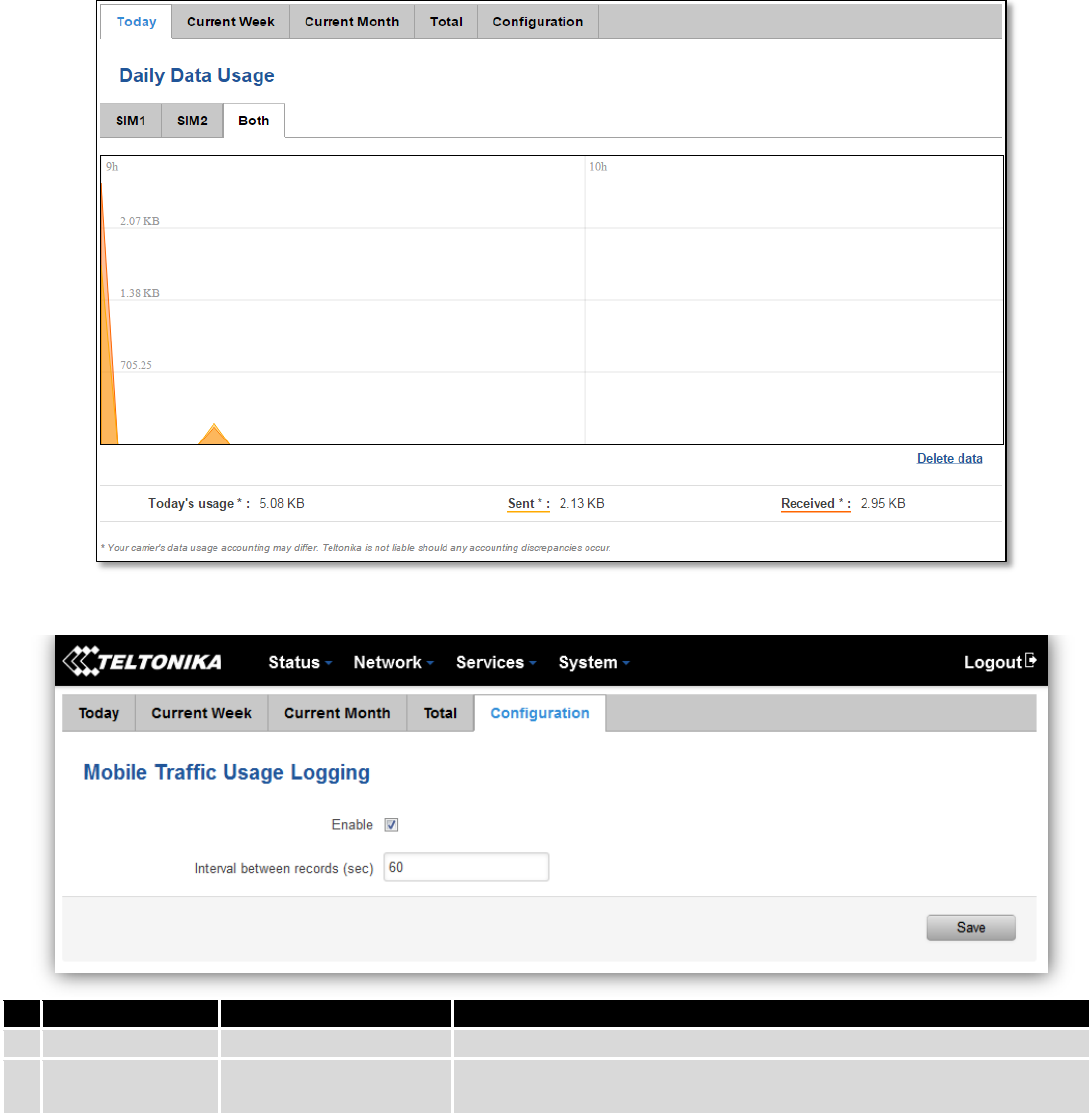
6.8 Mobile Traffic ........................................................................................................................................... 38
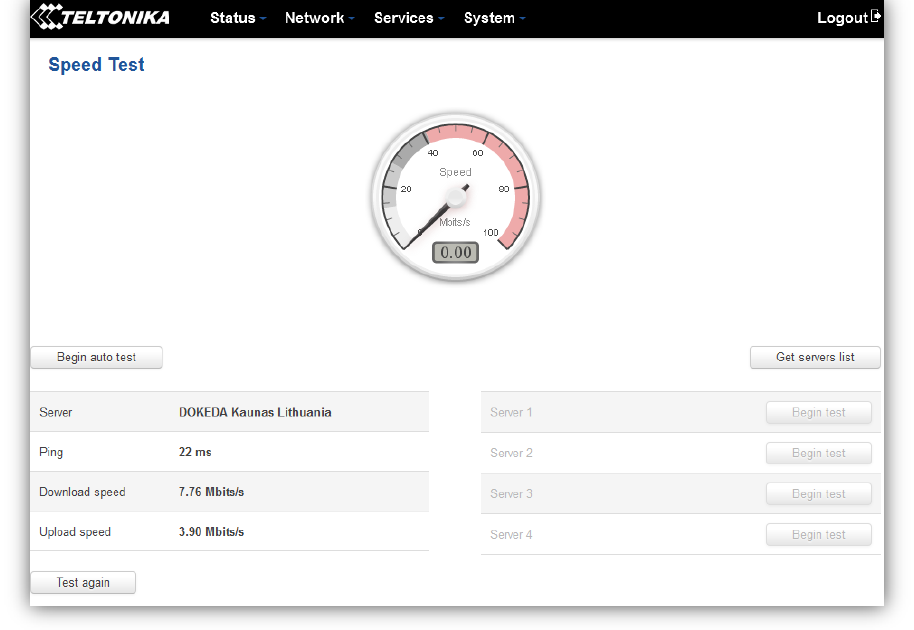
6.9 Speed Test ................................................................................................................................................ 38
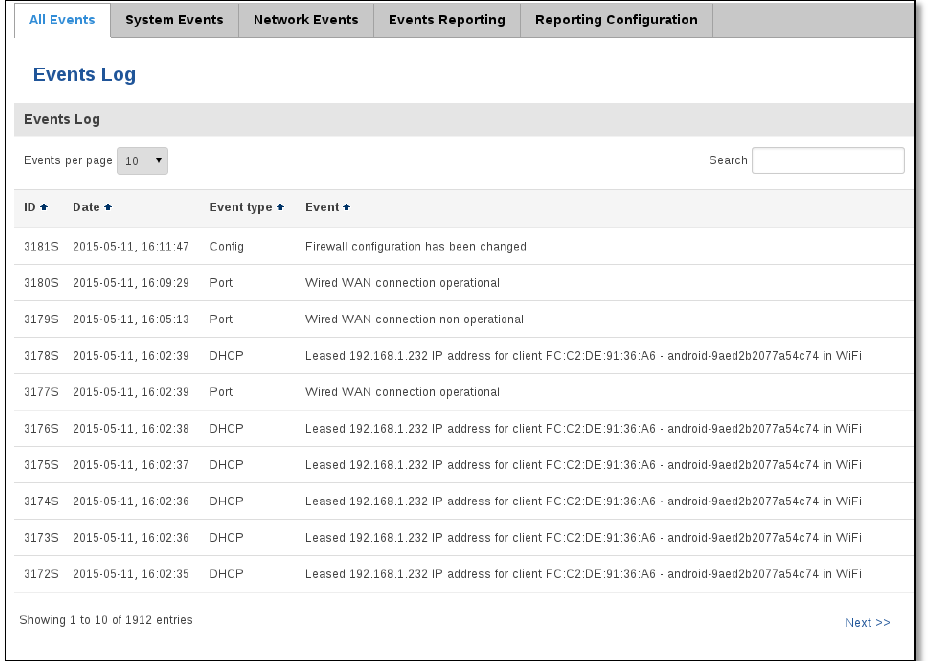
6.10 Events Log ............................................................................................................................................ 39
6.10.1 All Events ......................................................................................................................................... 39
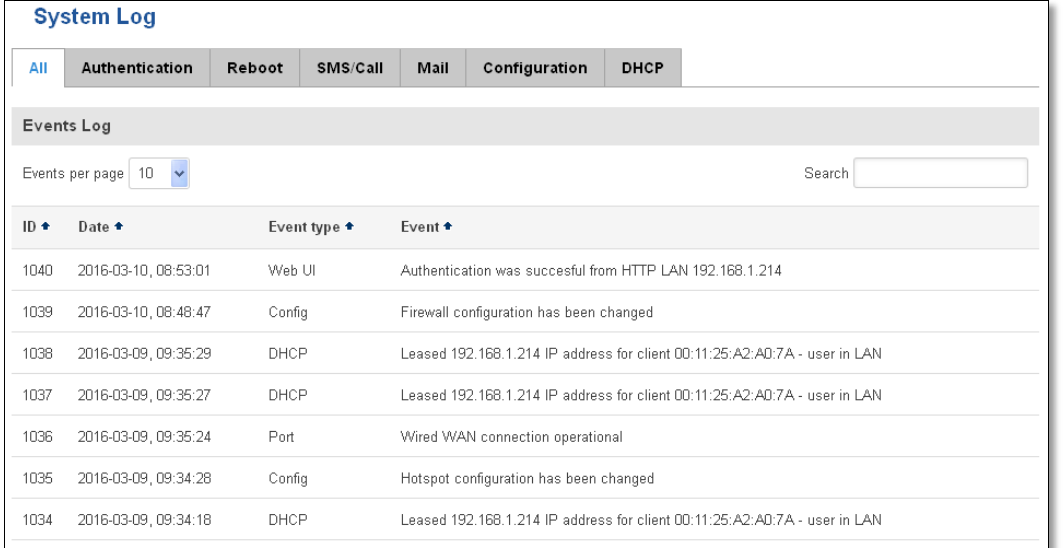
6.10.2 System Events .................................................................................................................................. 41
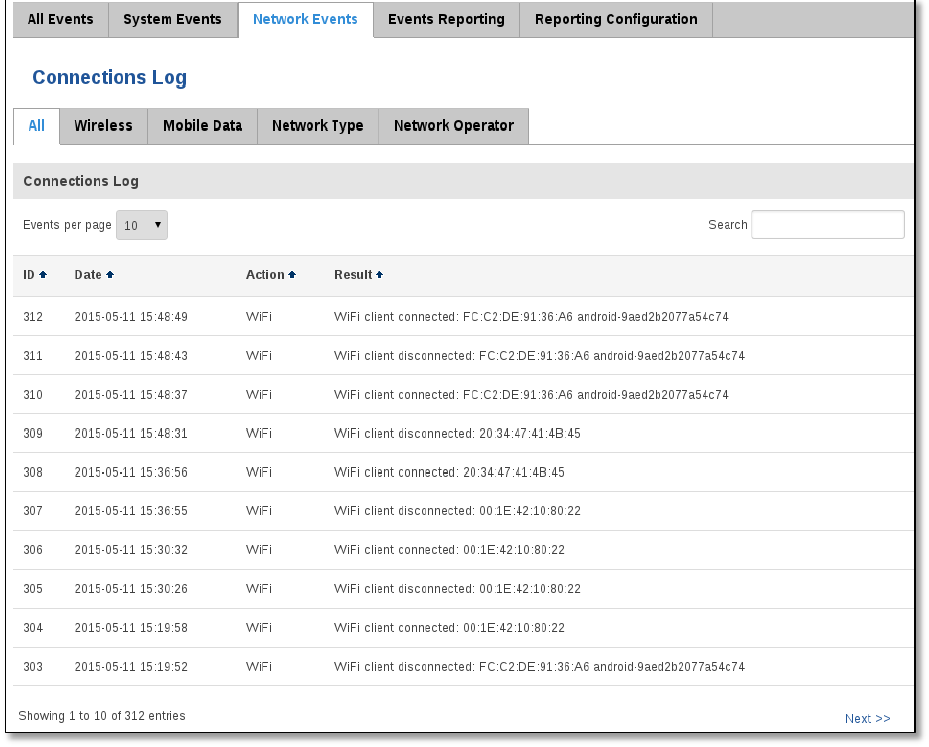
6.10.3 Network Events ............................................................................................................................... 42
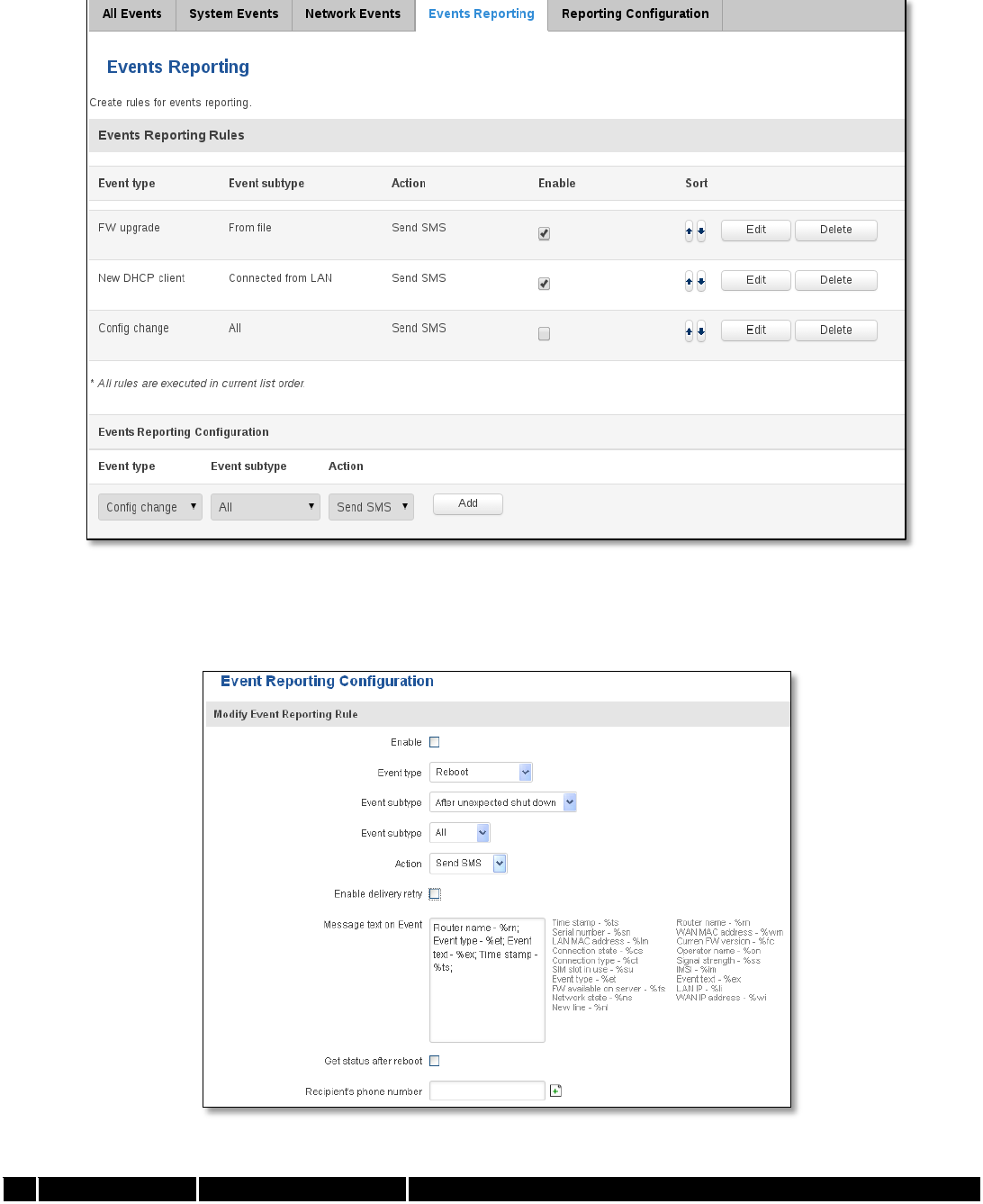
6.10.4 Events Reporting ............................................................................................................................. 43
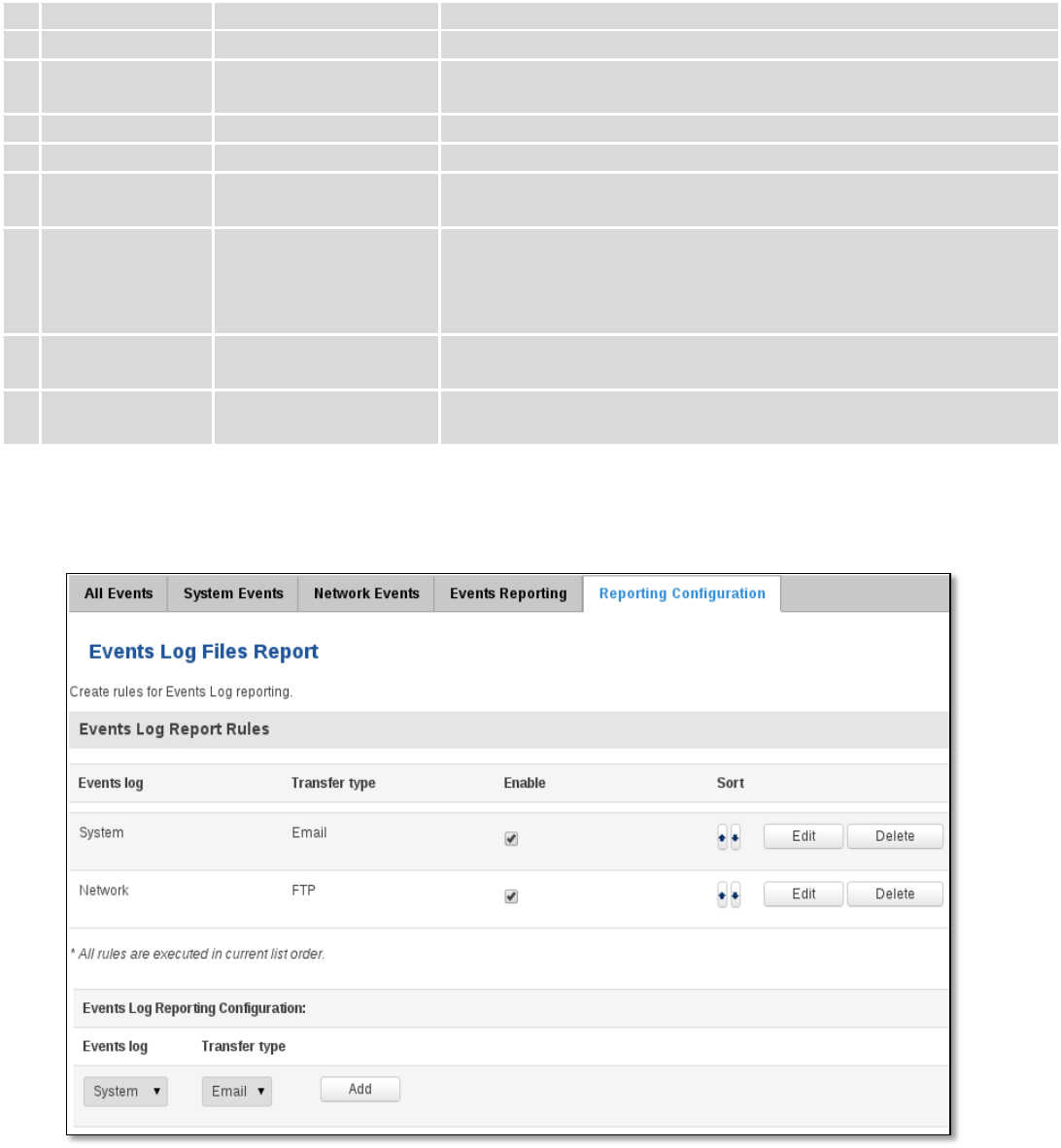
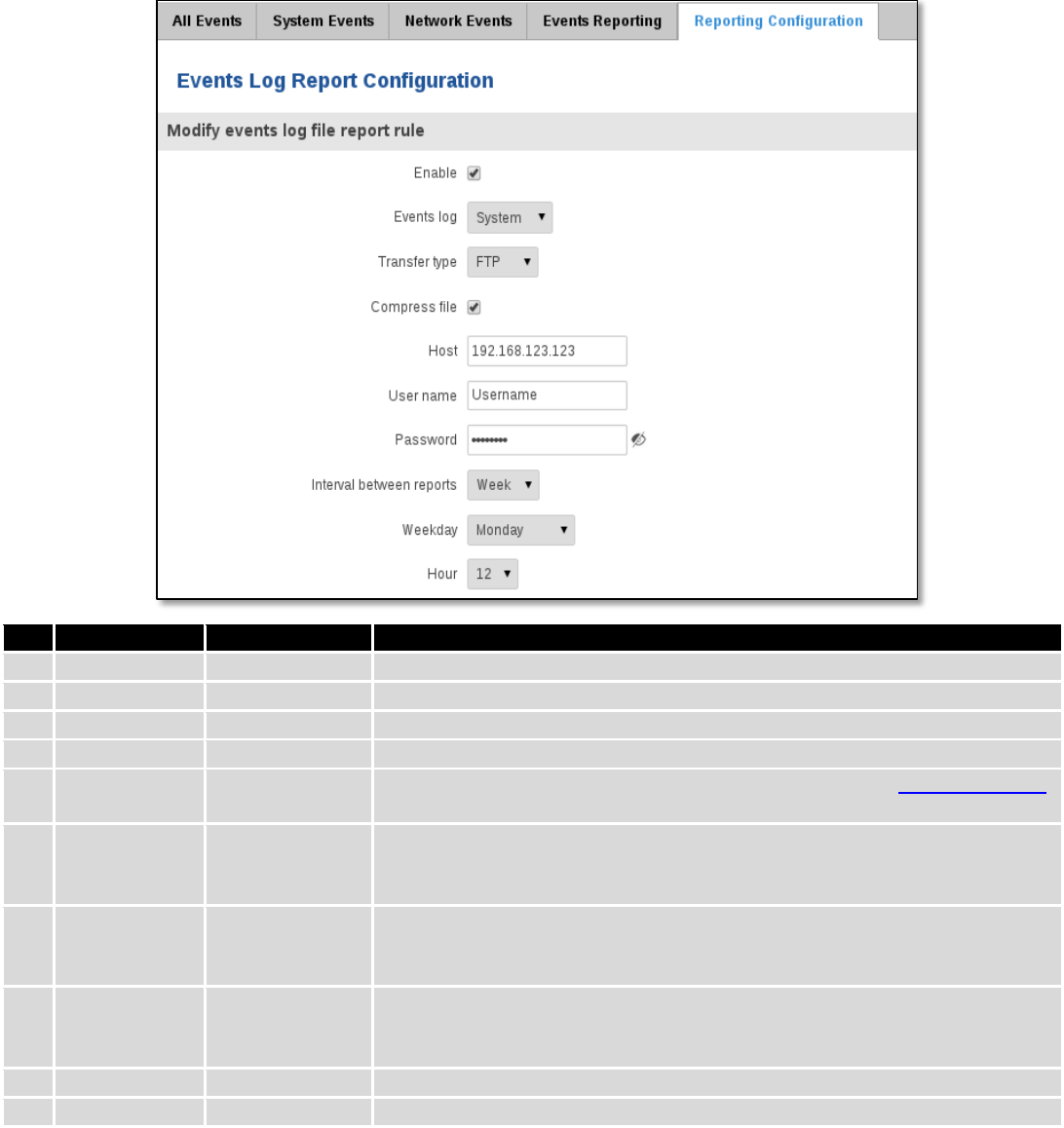
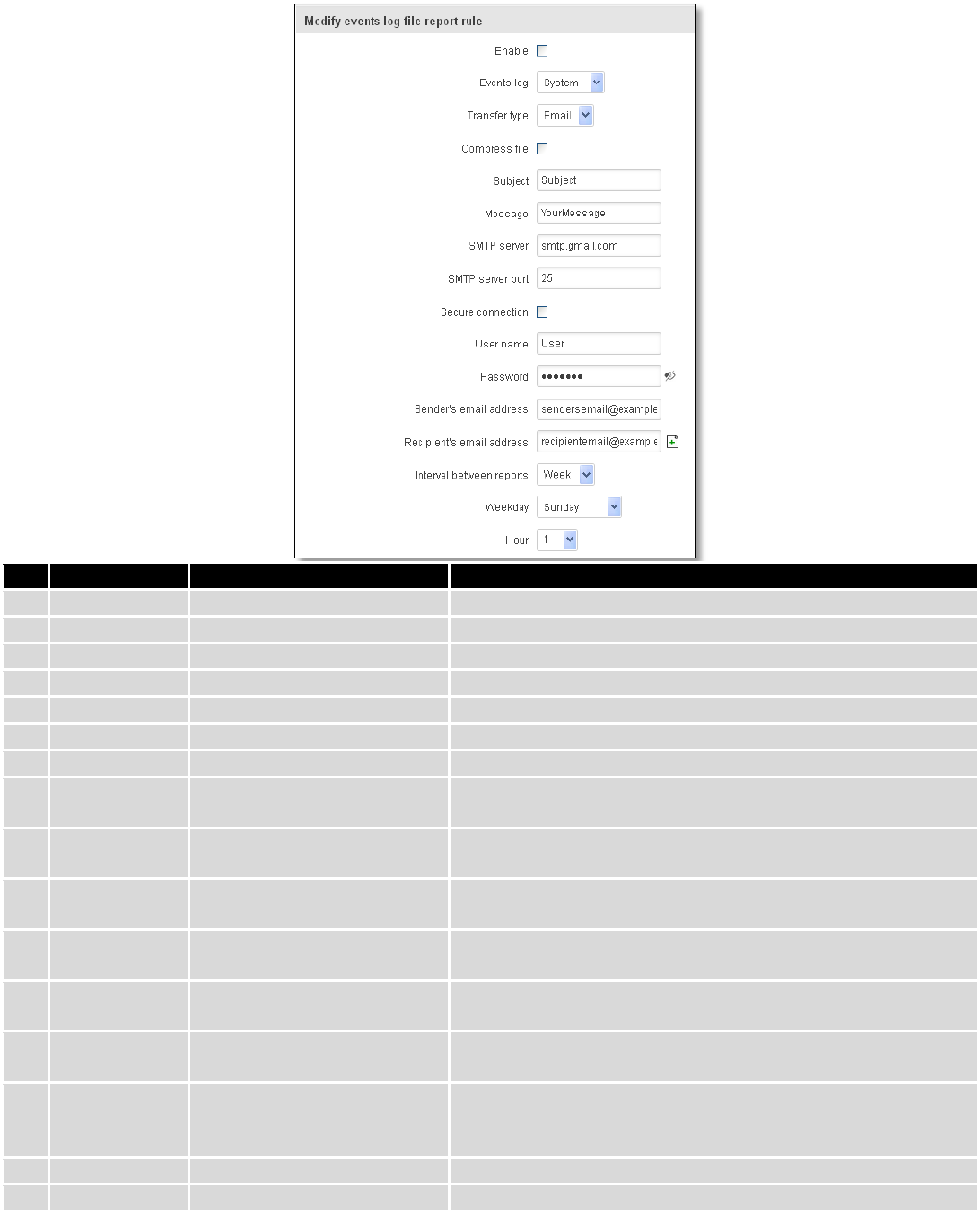
6.10.5 Reporting Configuration .................................................................................................................. 44
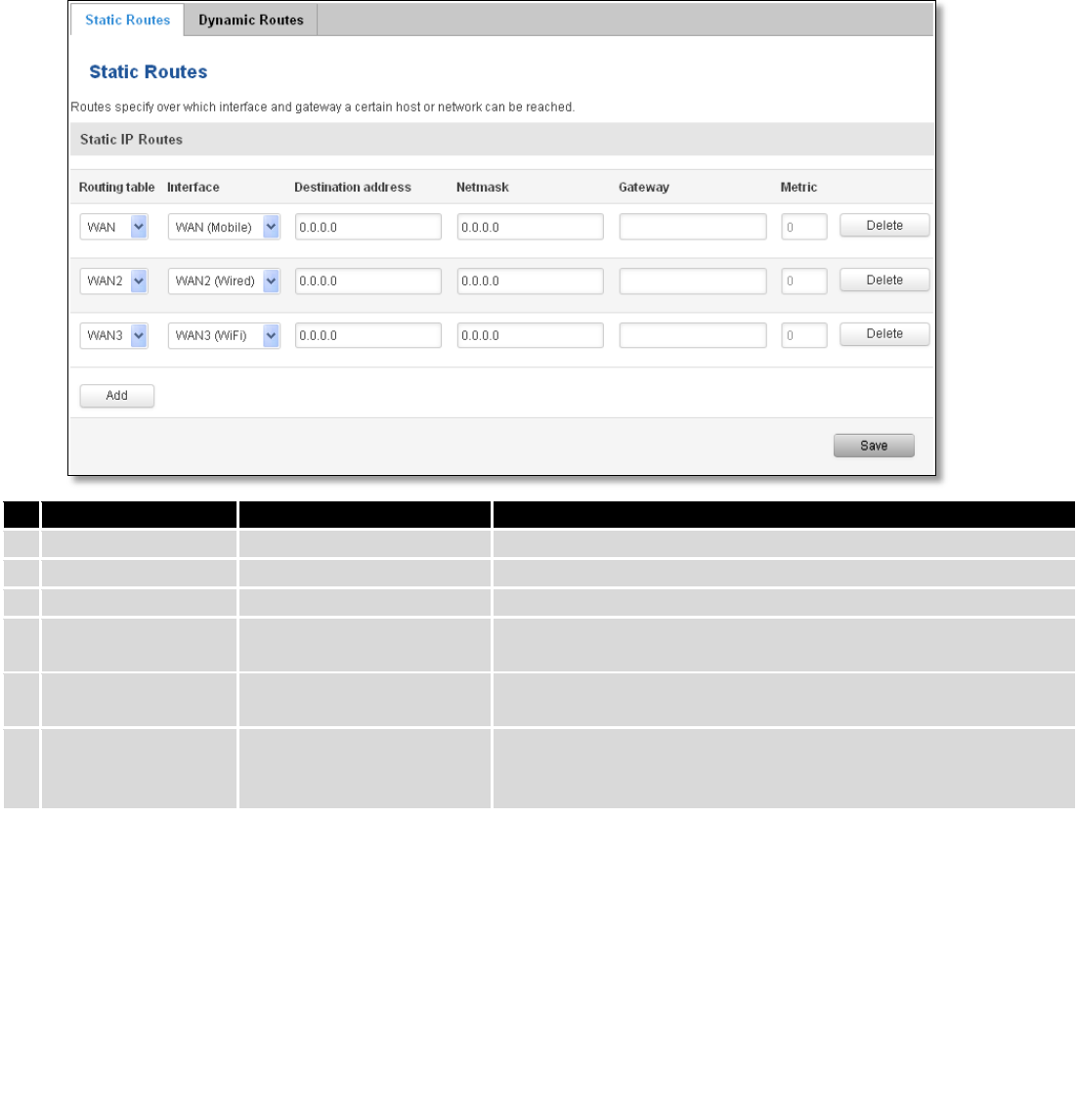
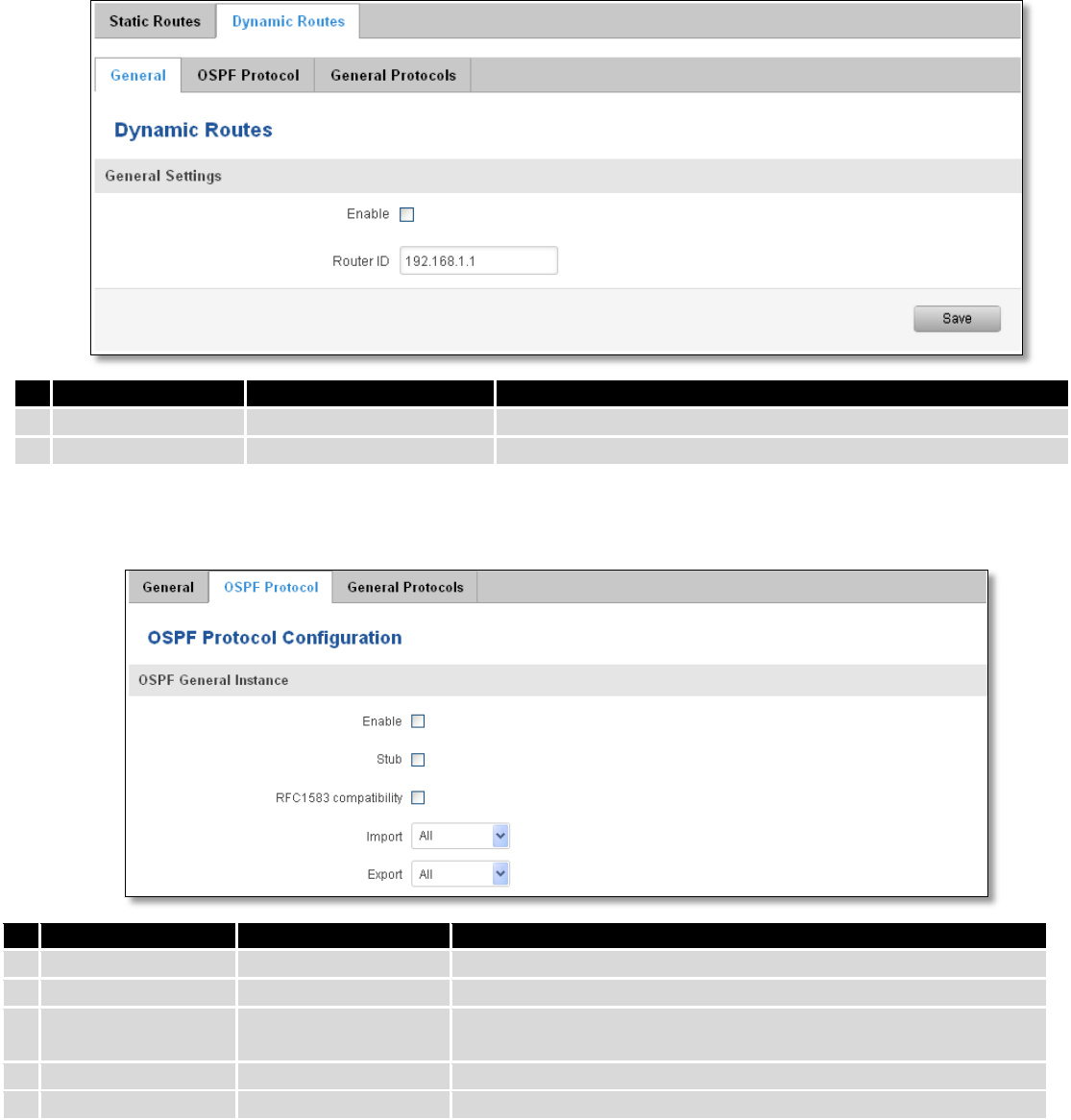
7 Network ....................................................................................................................................................... 47
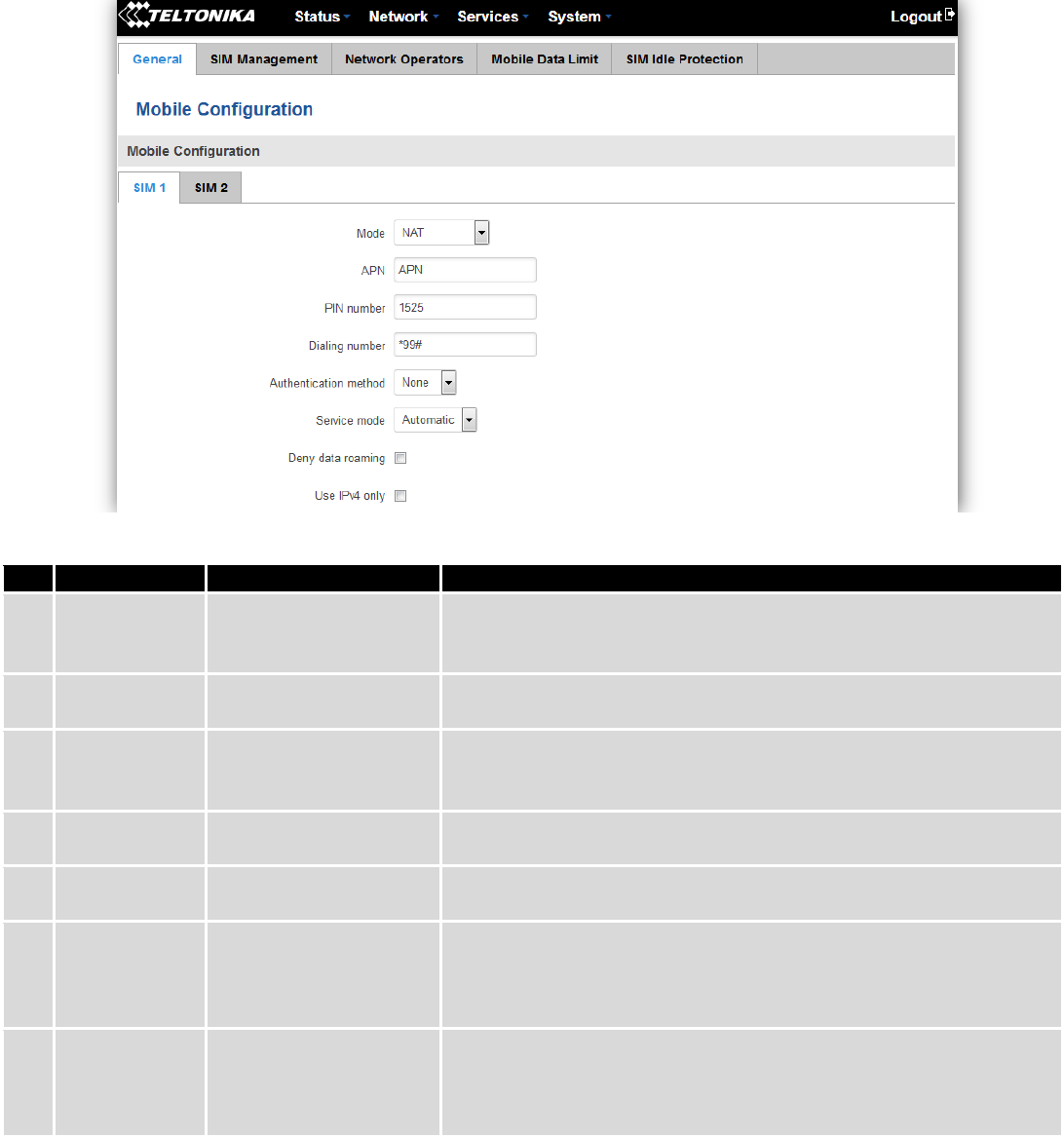
7.1 Mobile ...................................................................................................................................................... 47
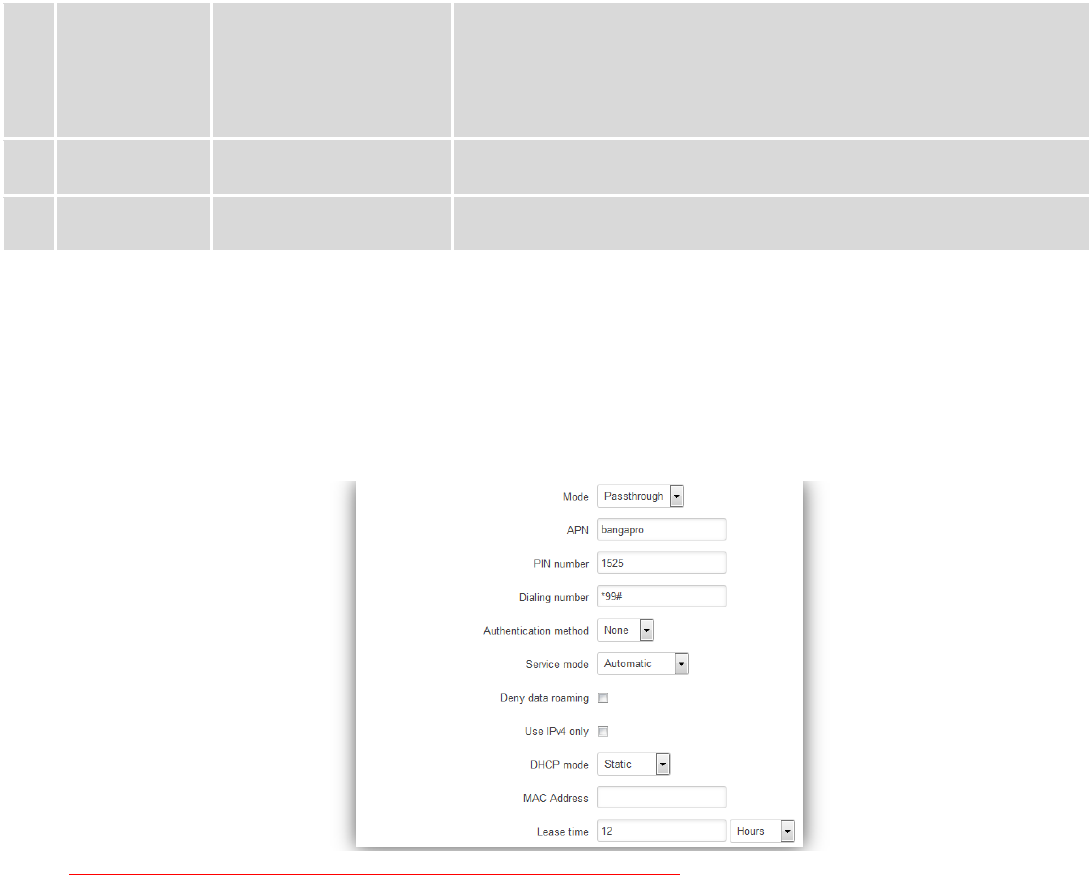
7.1.1 General ............................................................................................................................................. 47
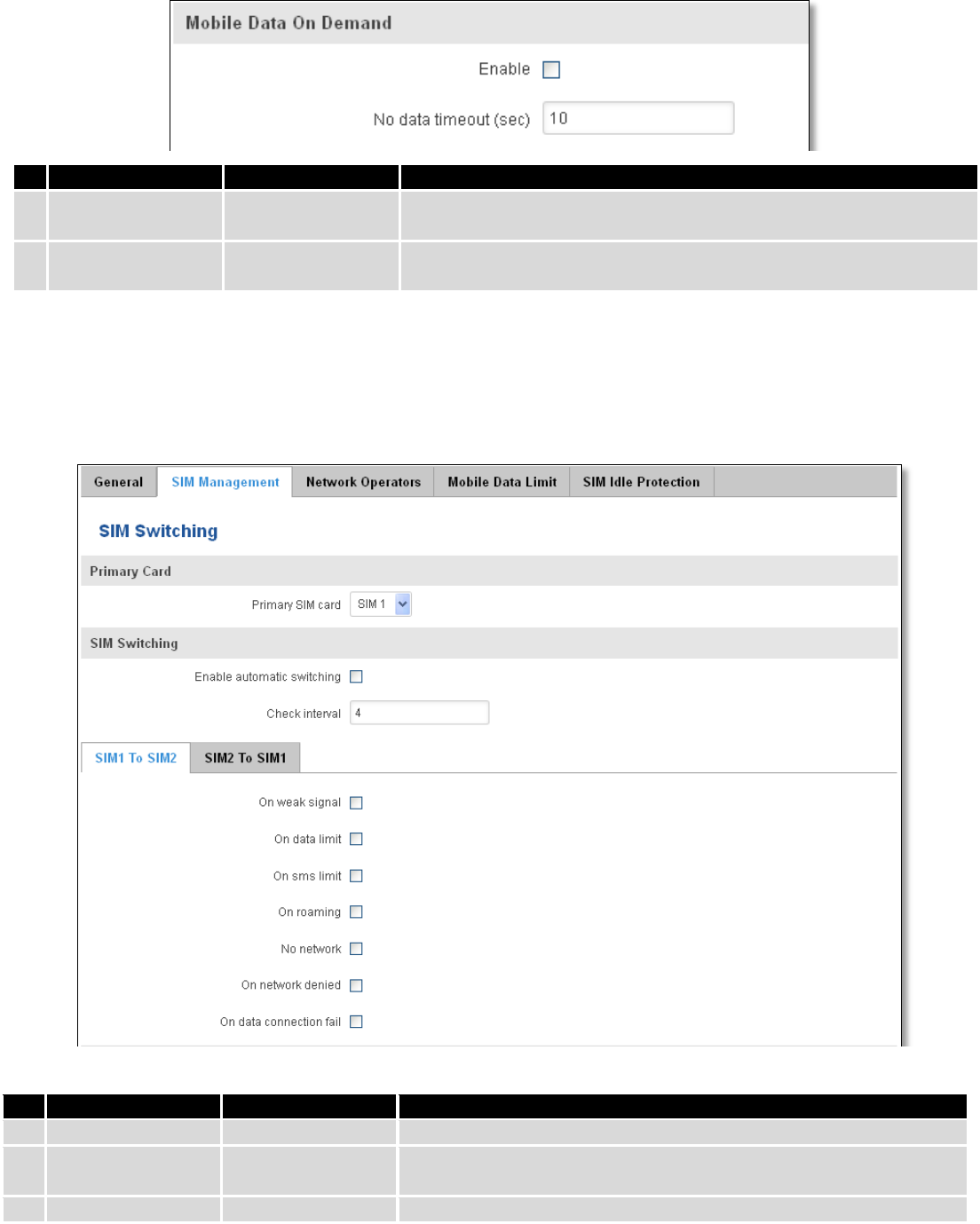
7.1.2 SIM Management ............................................................................................................................ 49
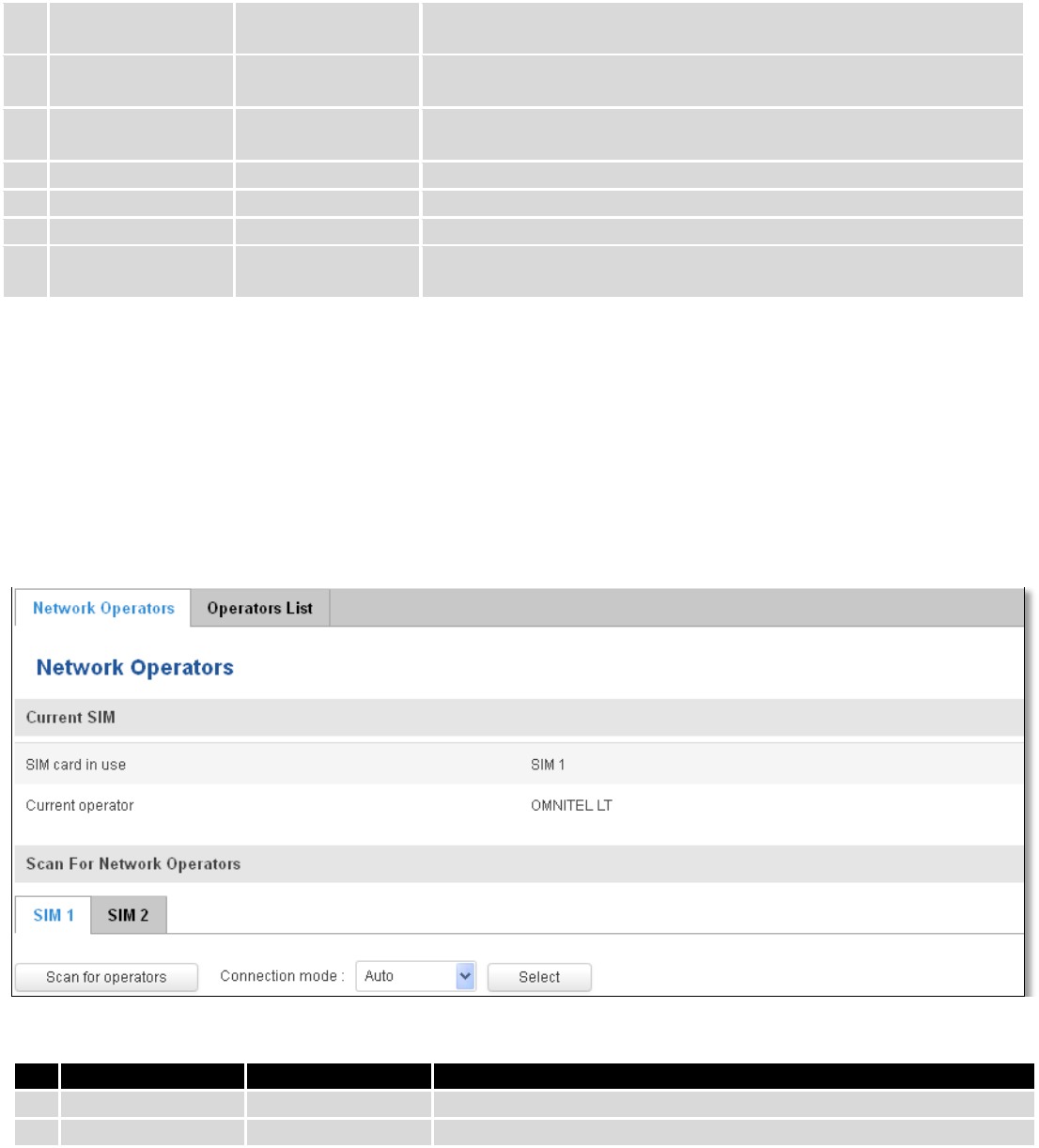
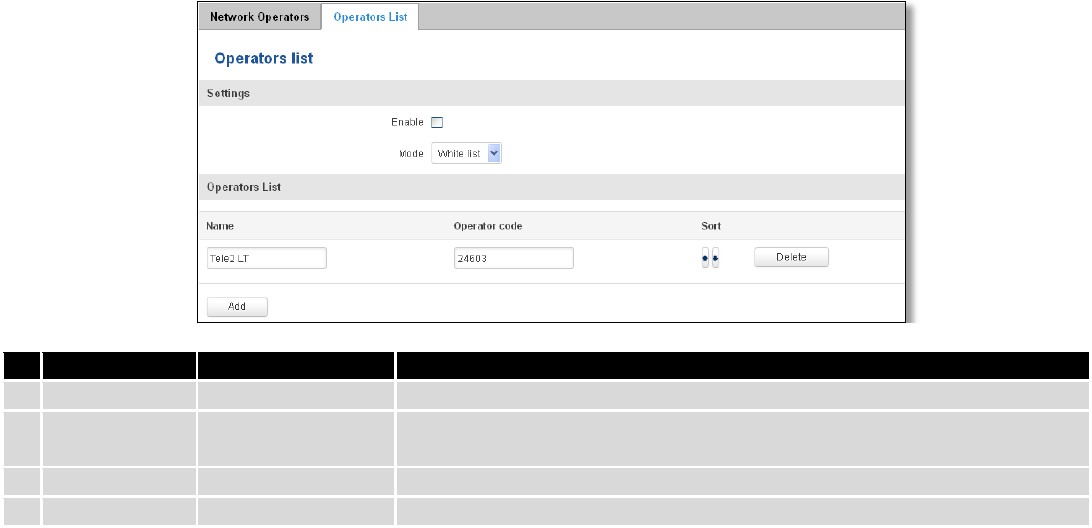
7.1.3 Network Operators .......................................................................................................................... 50
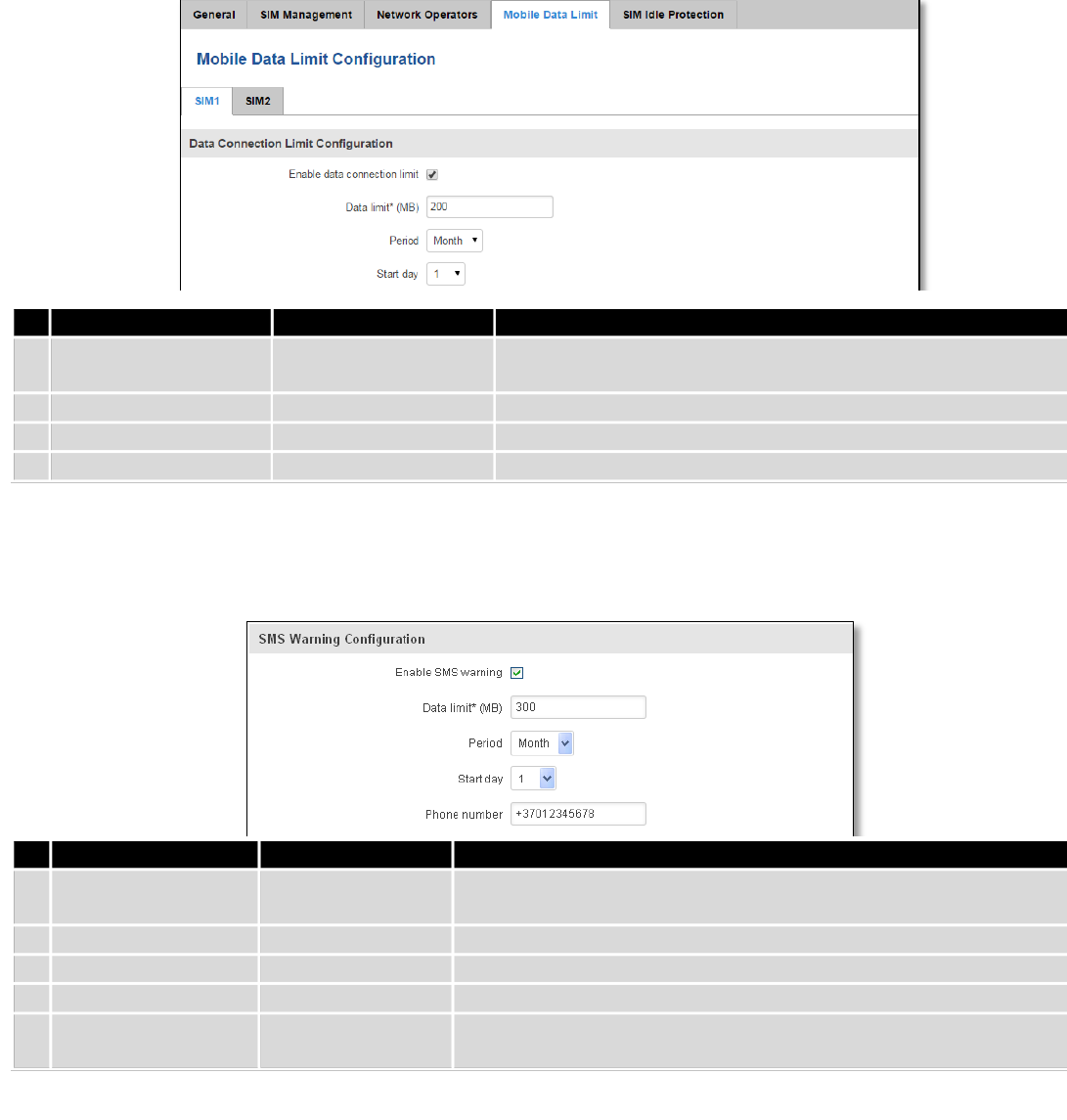
7.1.4 Mobile Data Limit............................................................................................................................. 51
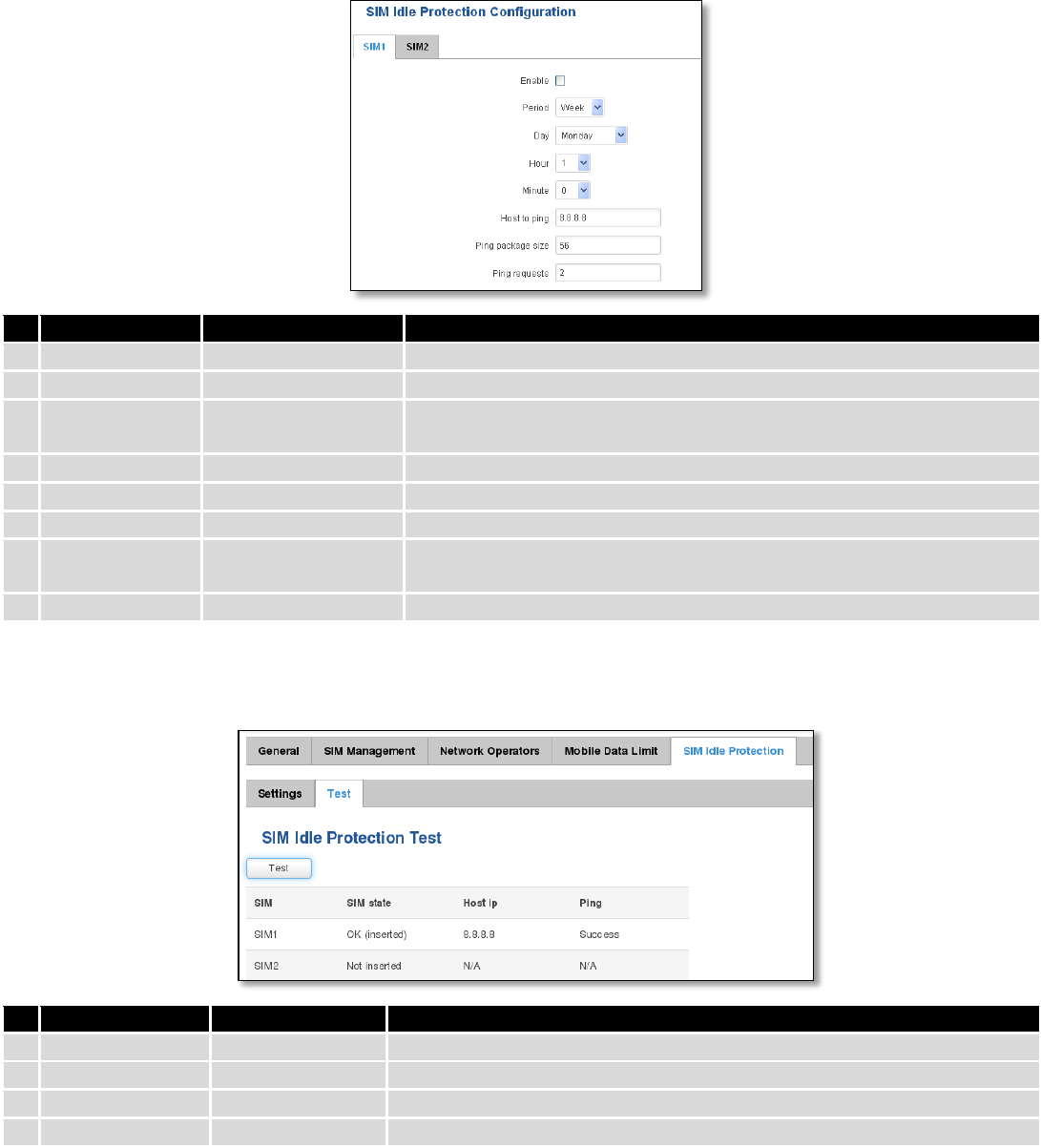
7.1.5 SIM Idle protection .......................................................................................................................... 52
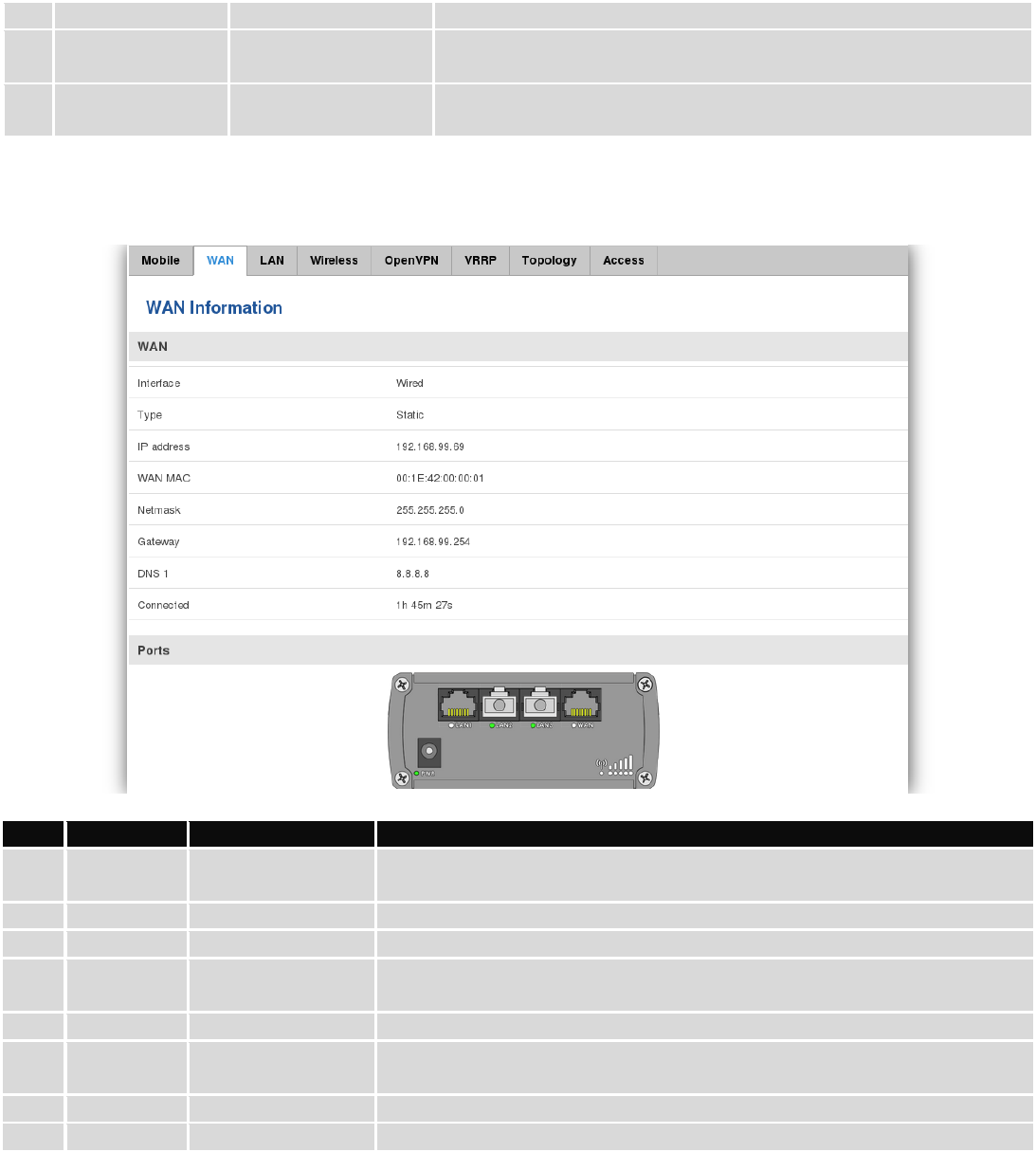
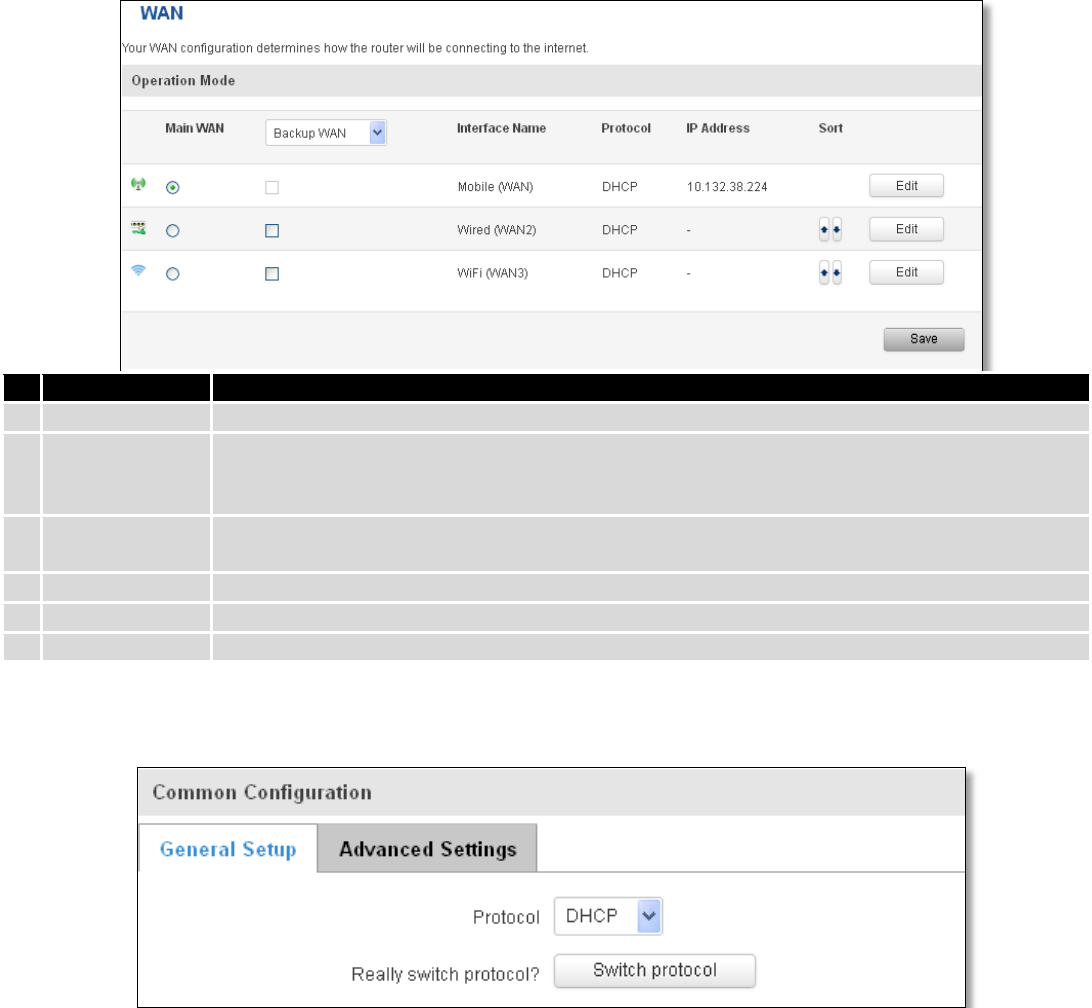
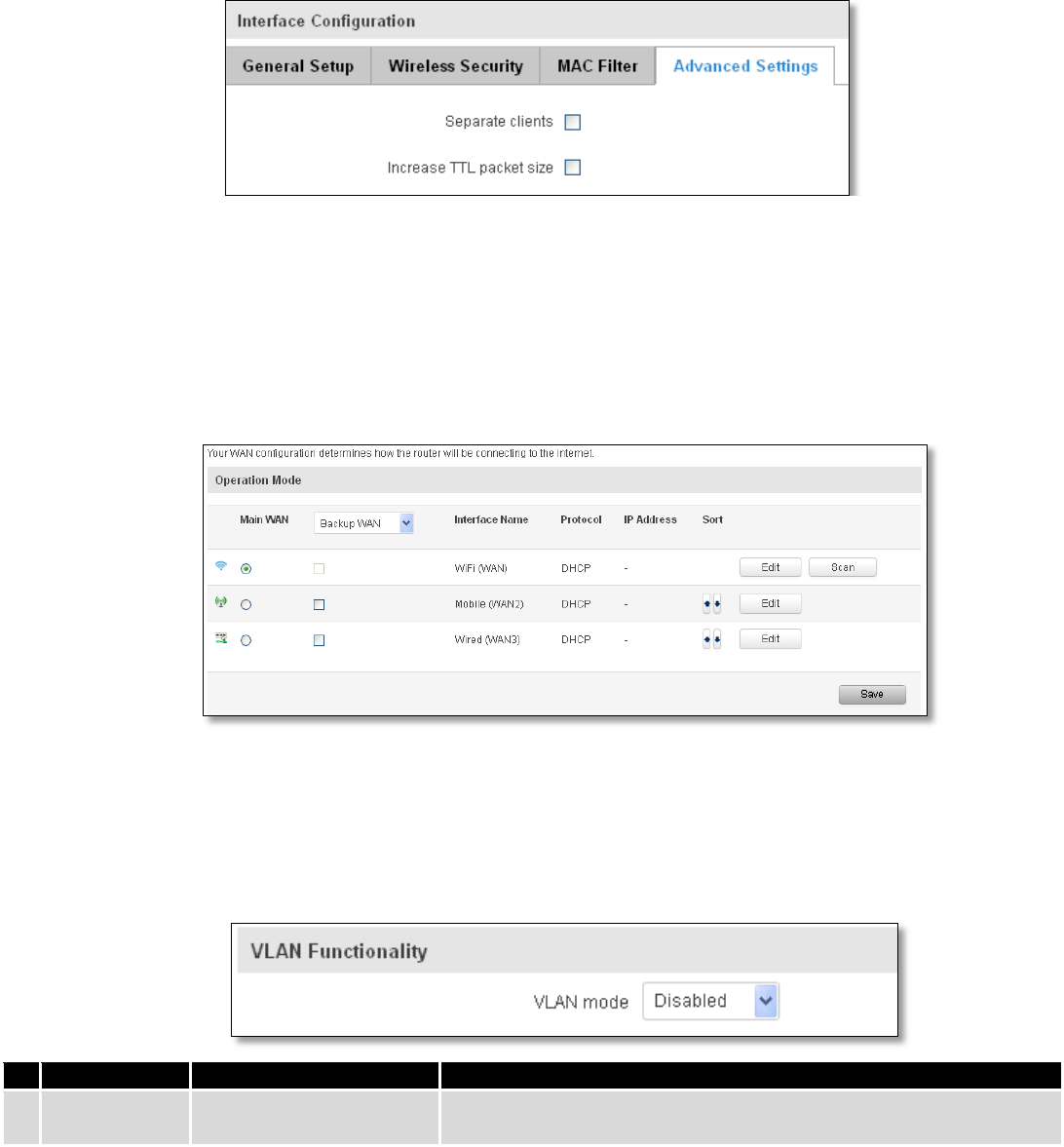
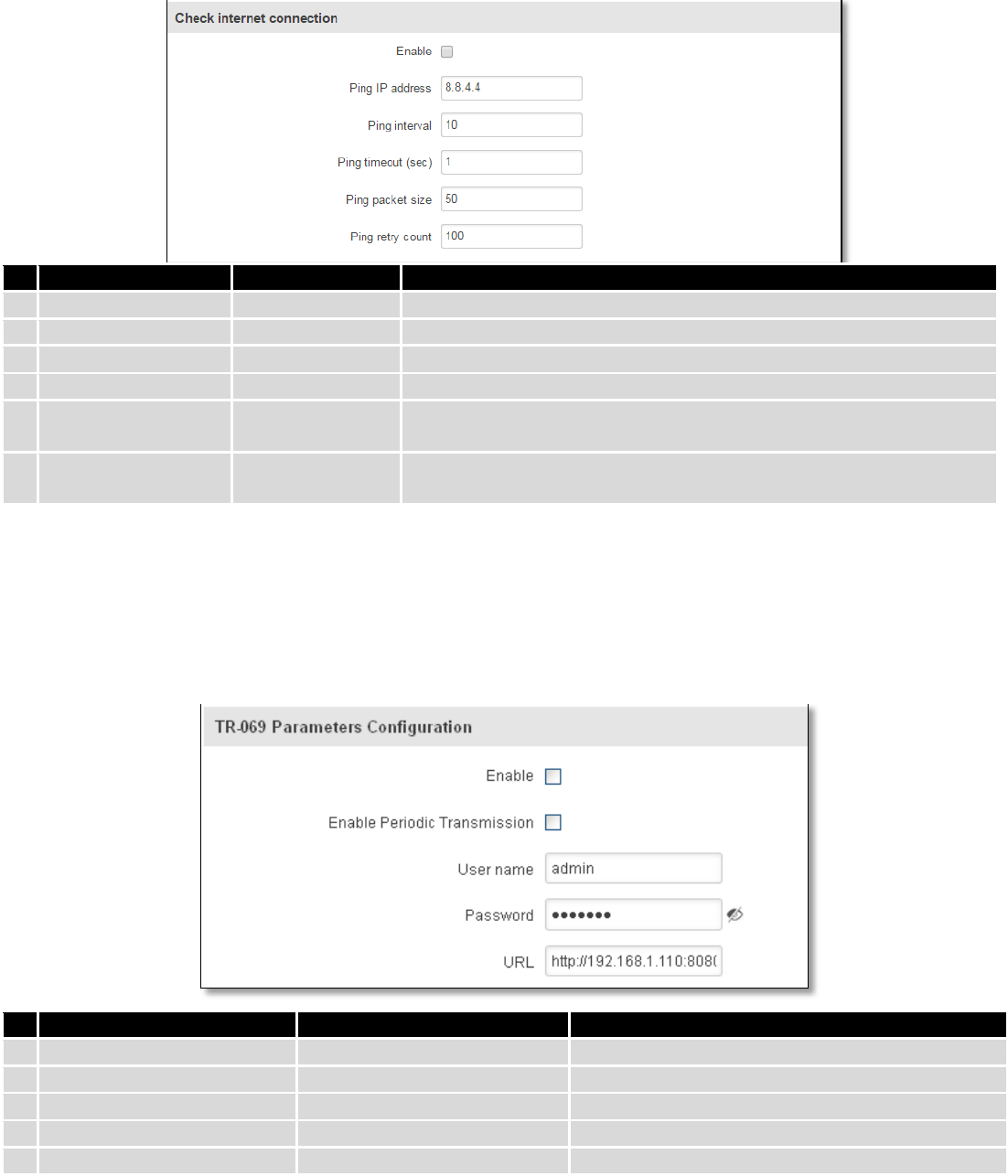
7.2 WAN ......................................................................................................................................................... 53
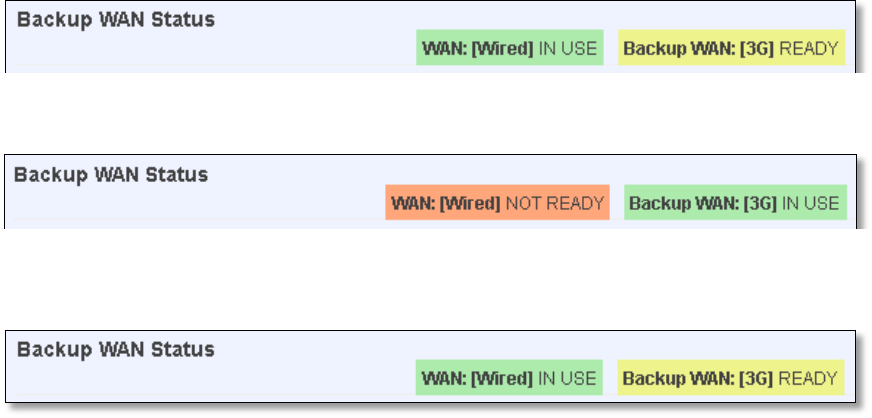
7.2.1 Operation Mode .............................................................................................................................. 53
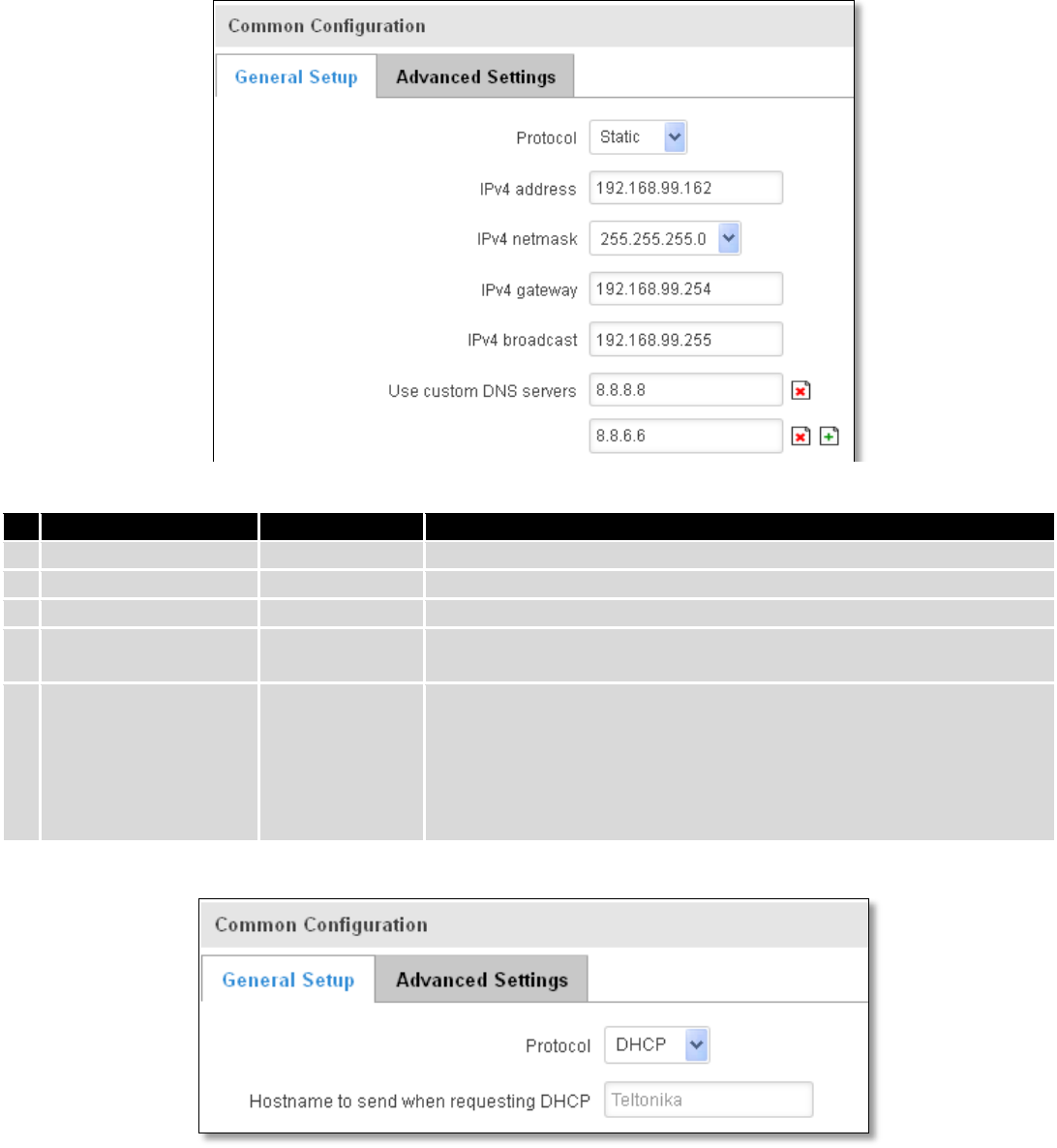
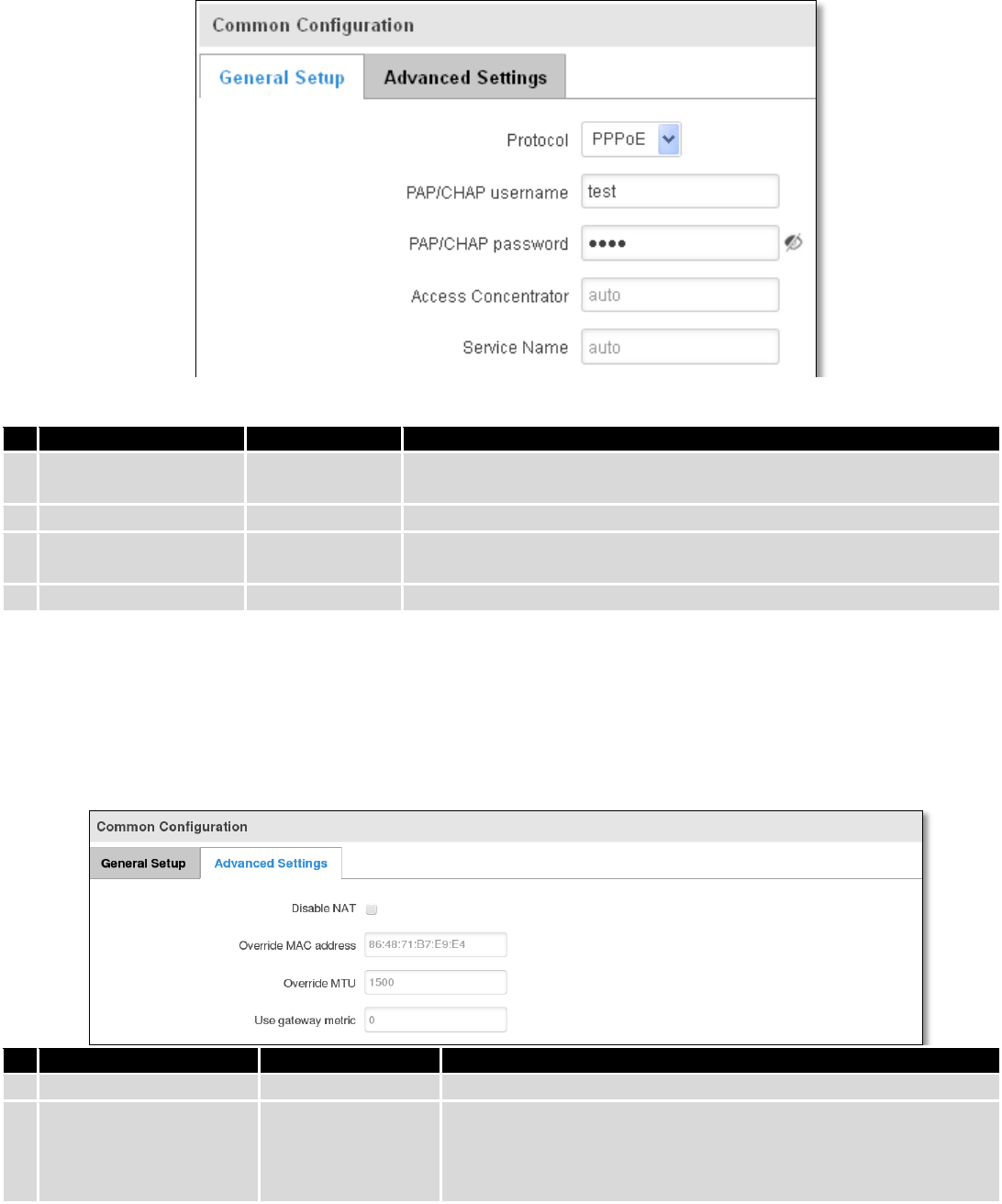
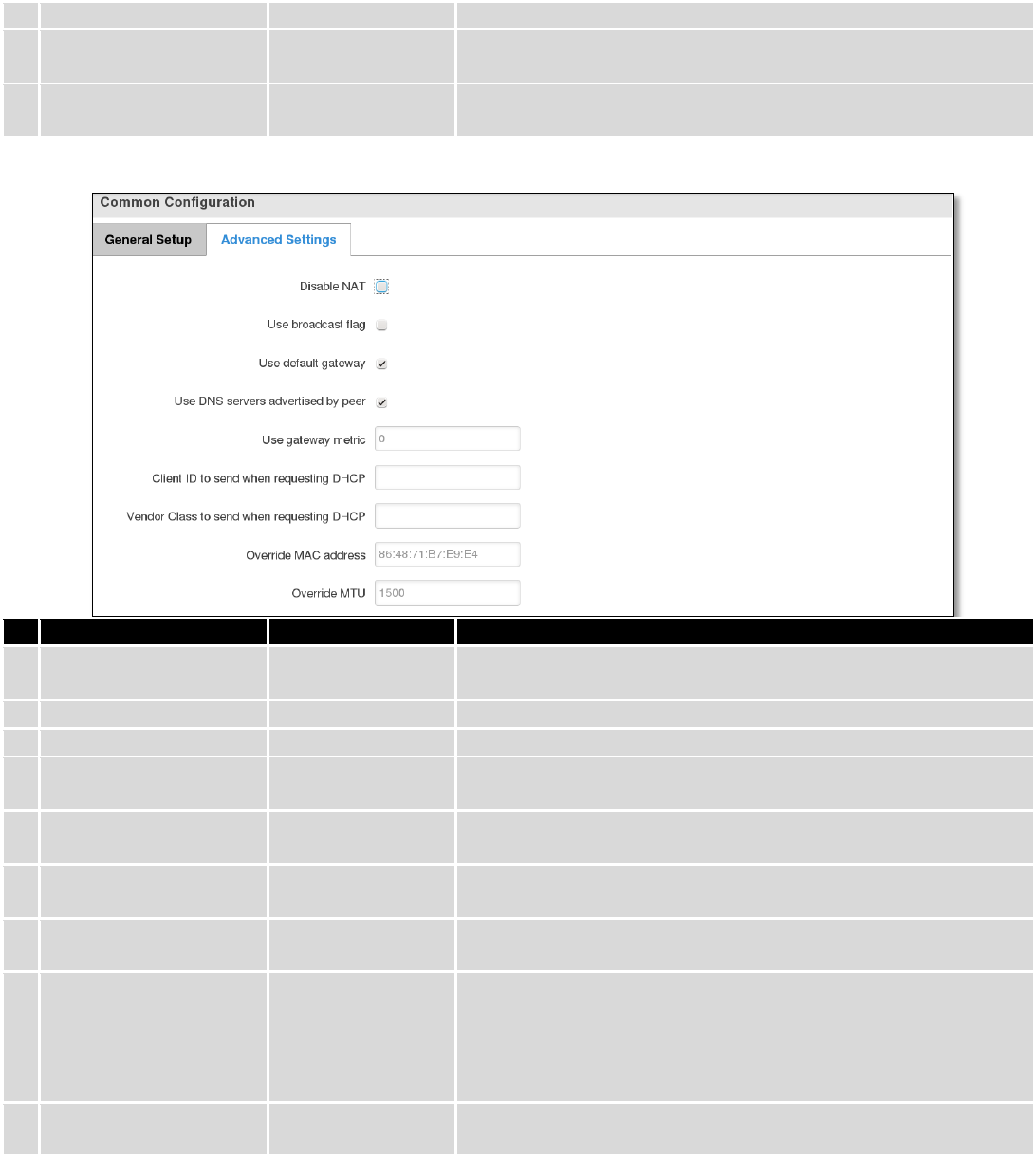
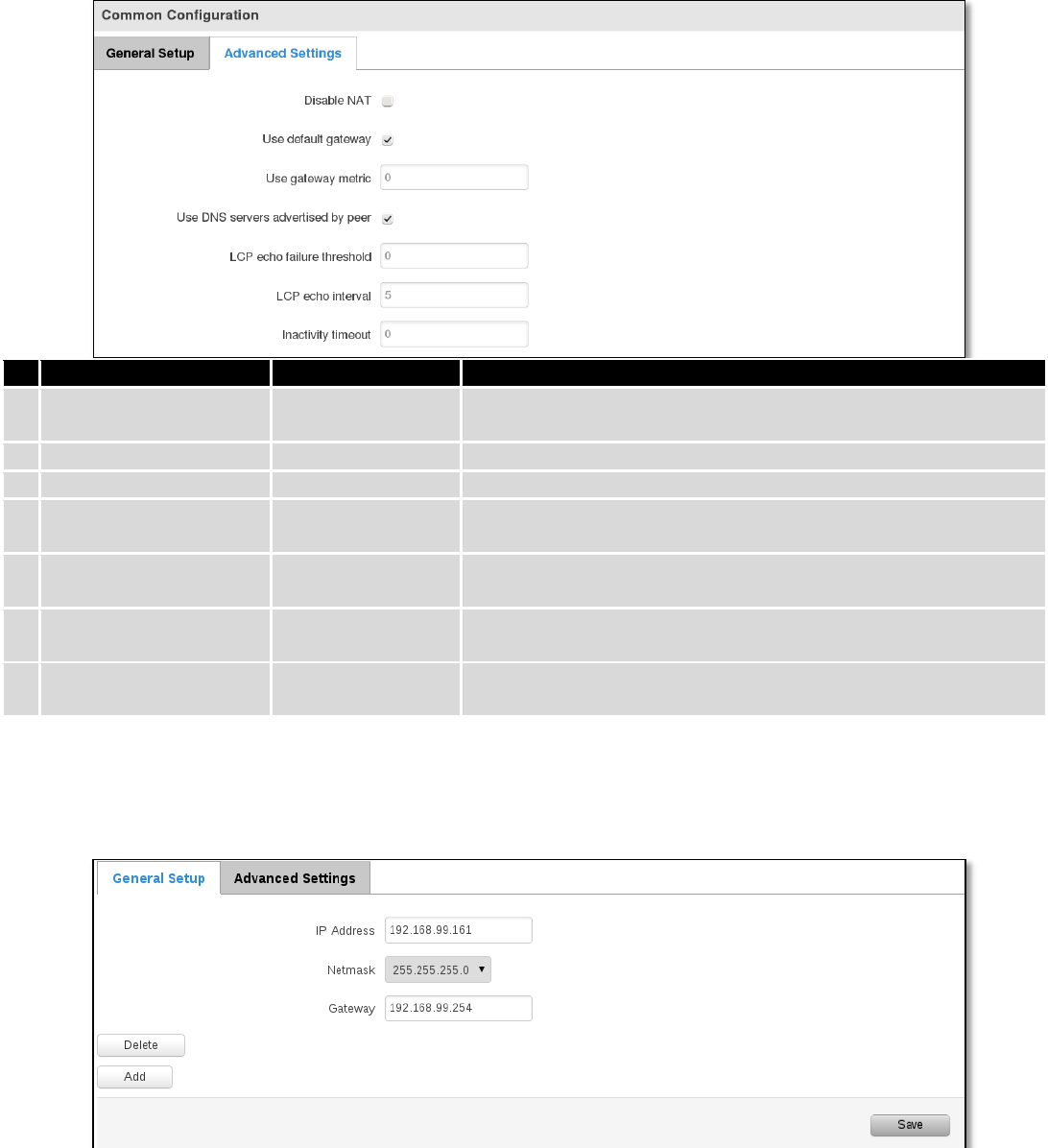
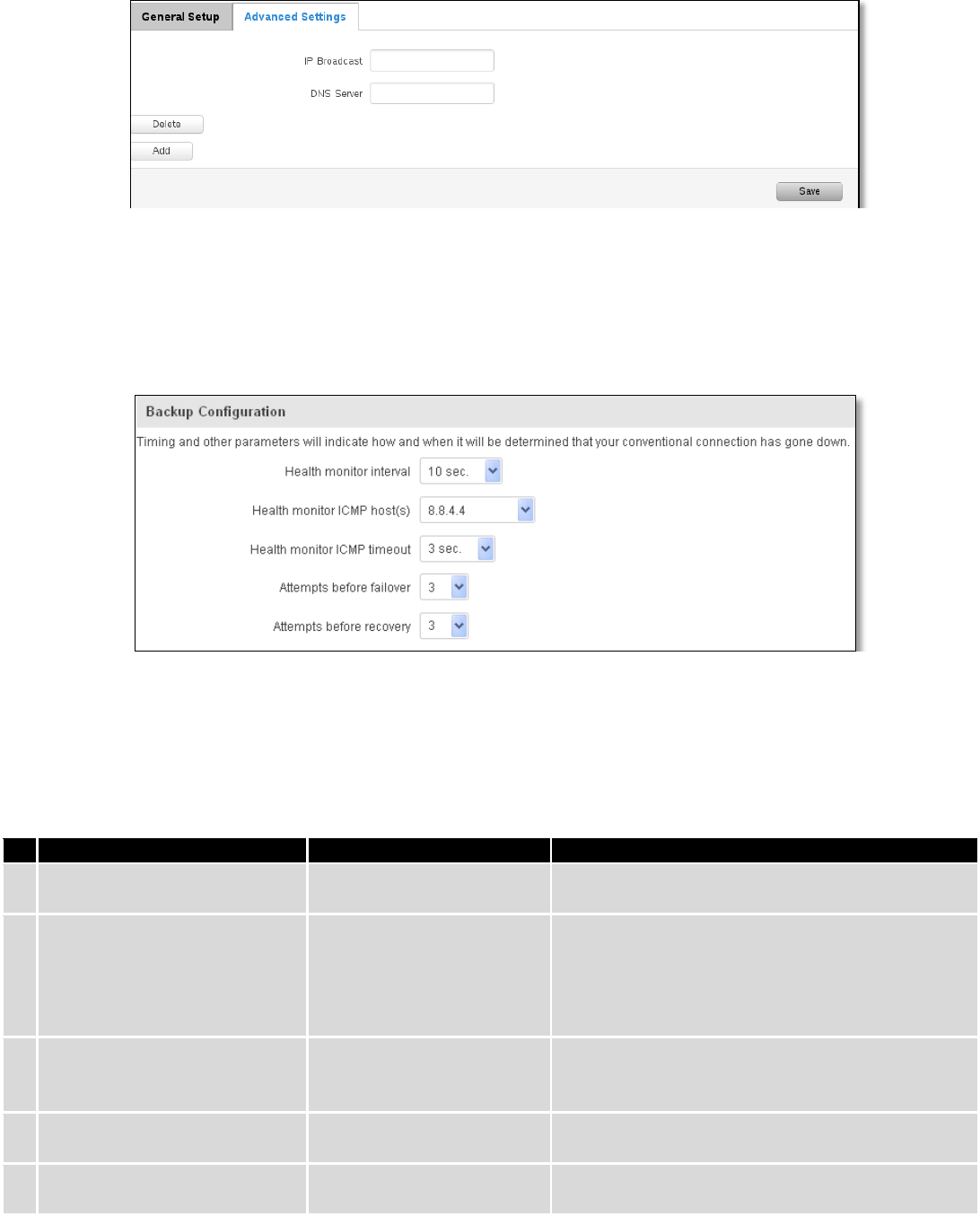
7.2.2 Common configuration .................................................................................................................... 54
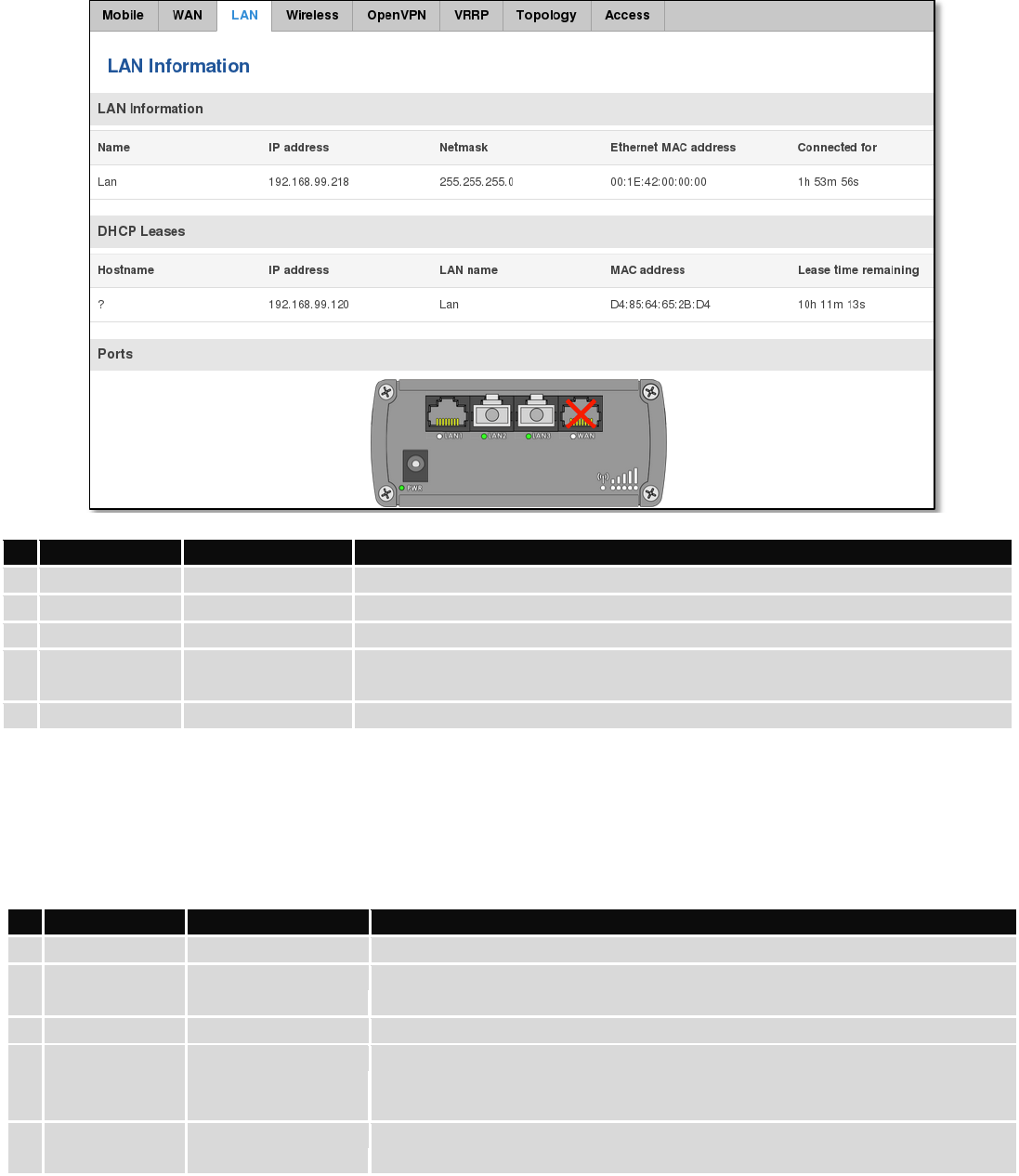
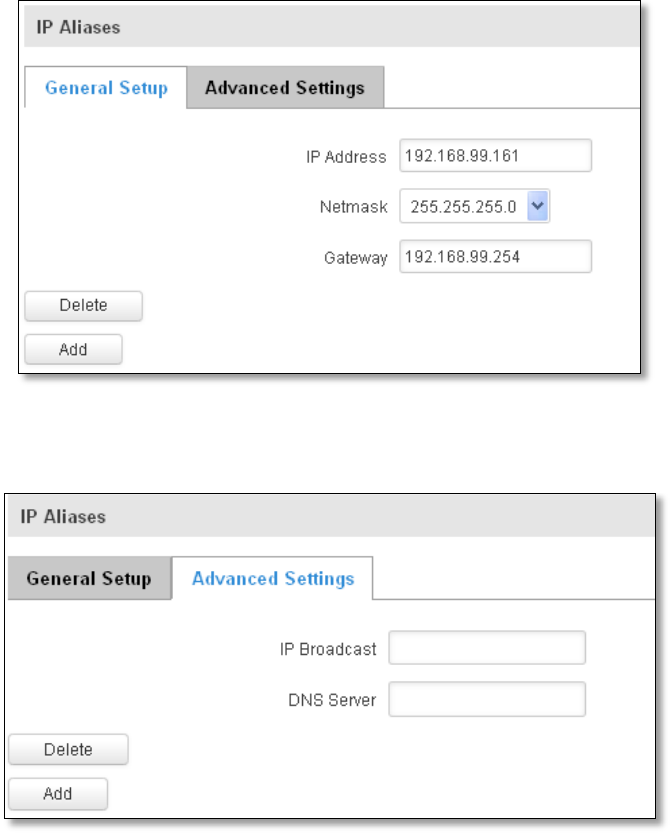
7.3 LAN ........................................................................................................................................................... 61
7.3.1 Configuration ................................................................................................................................... 61
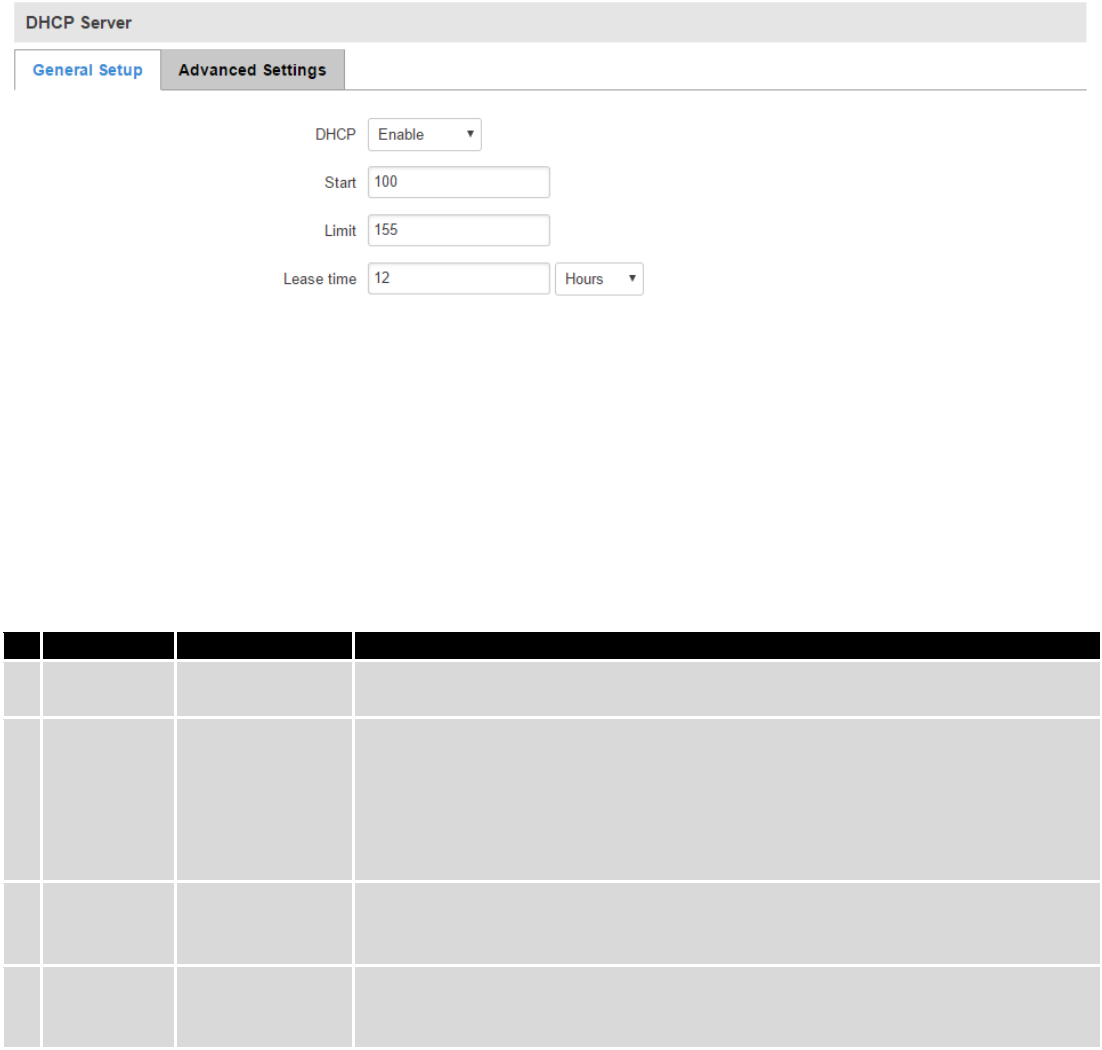
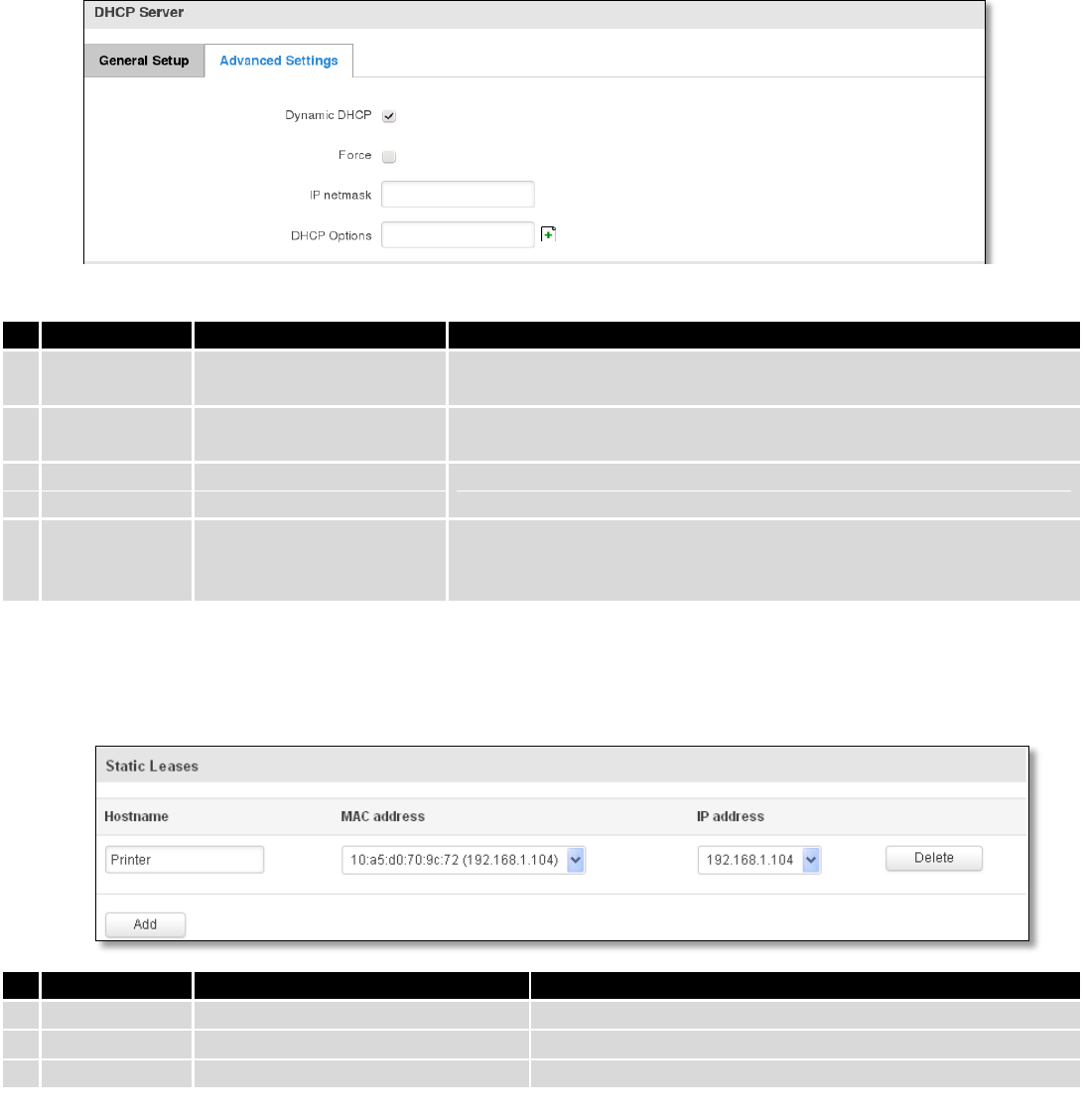
7.3.2 DHCP Server ..................................................................................................................................... 62
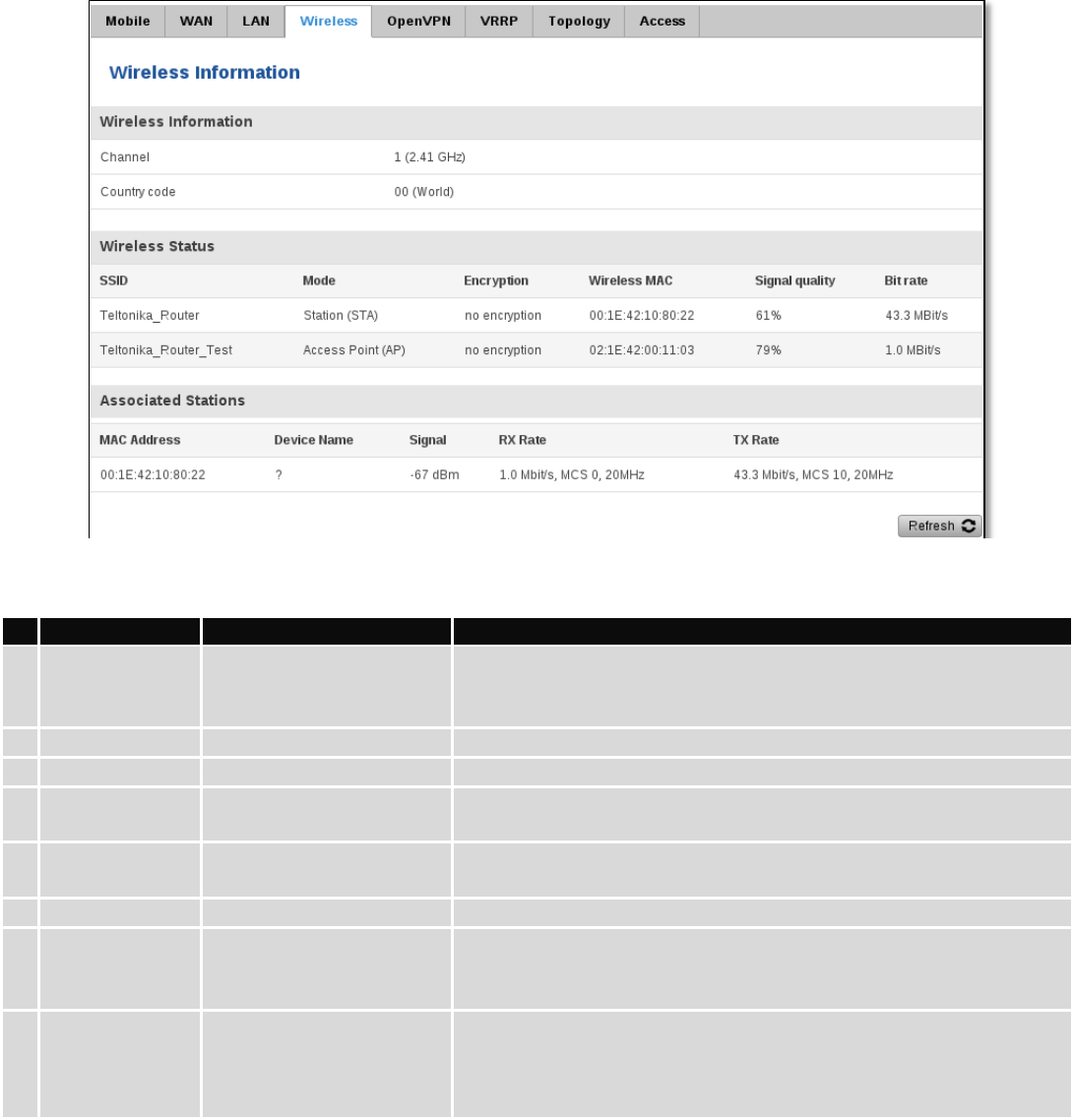
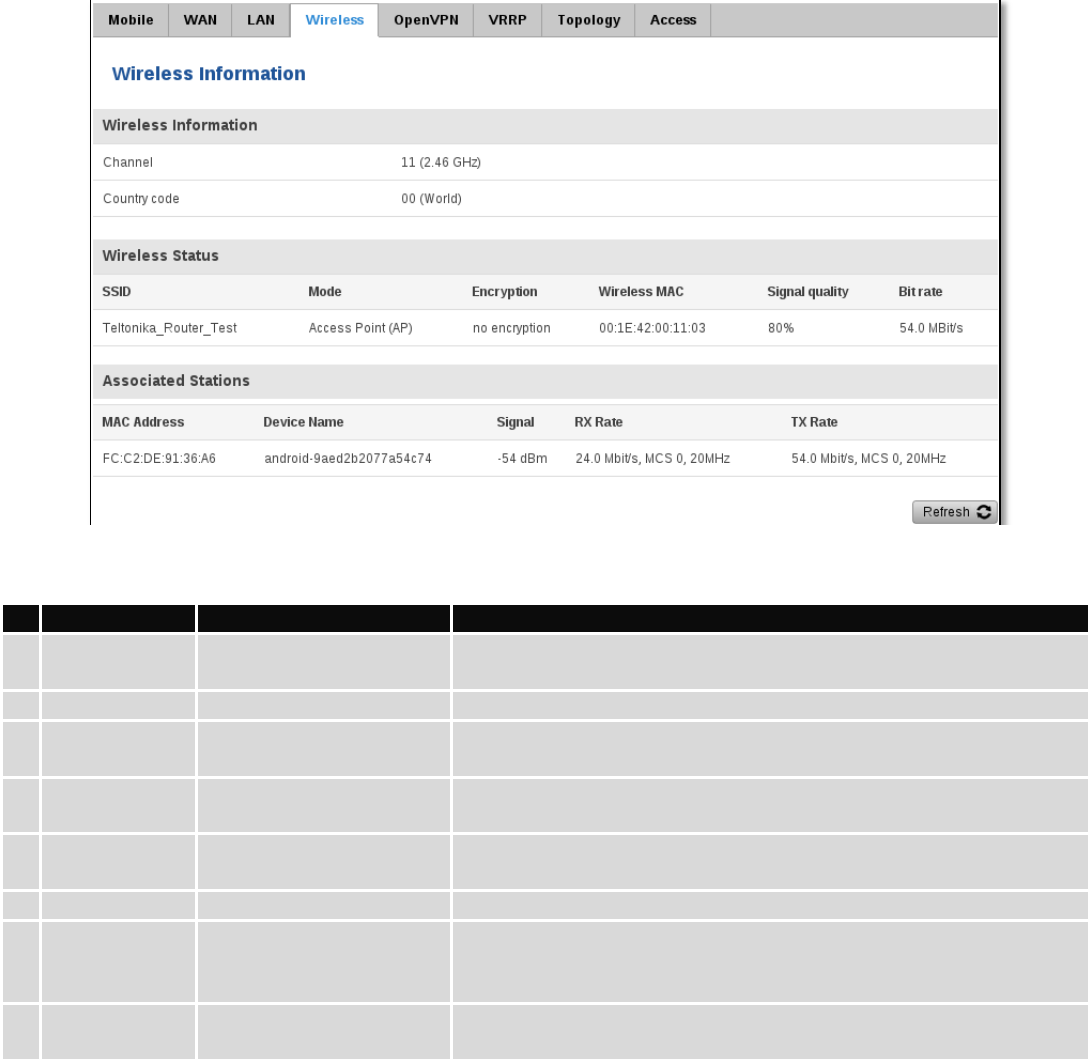
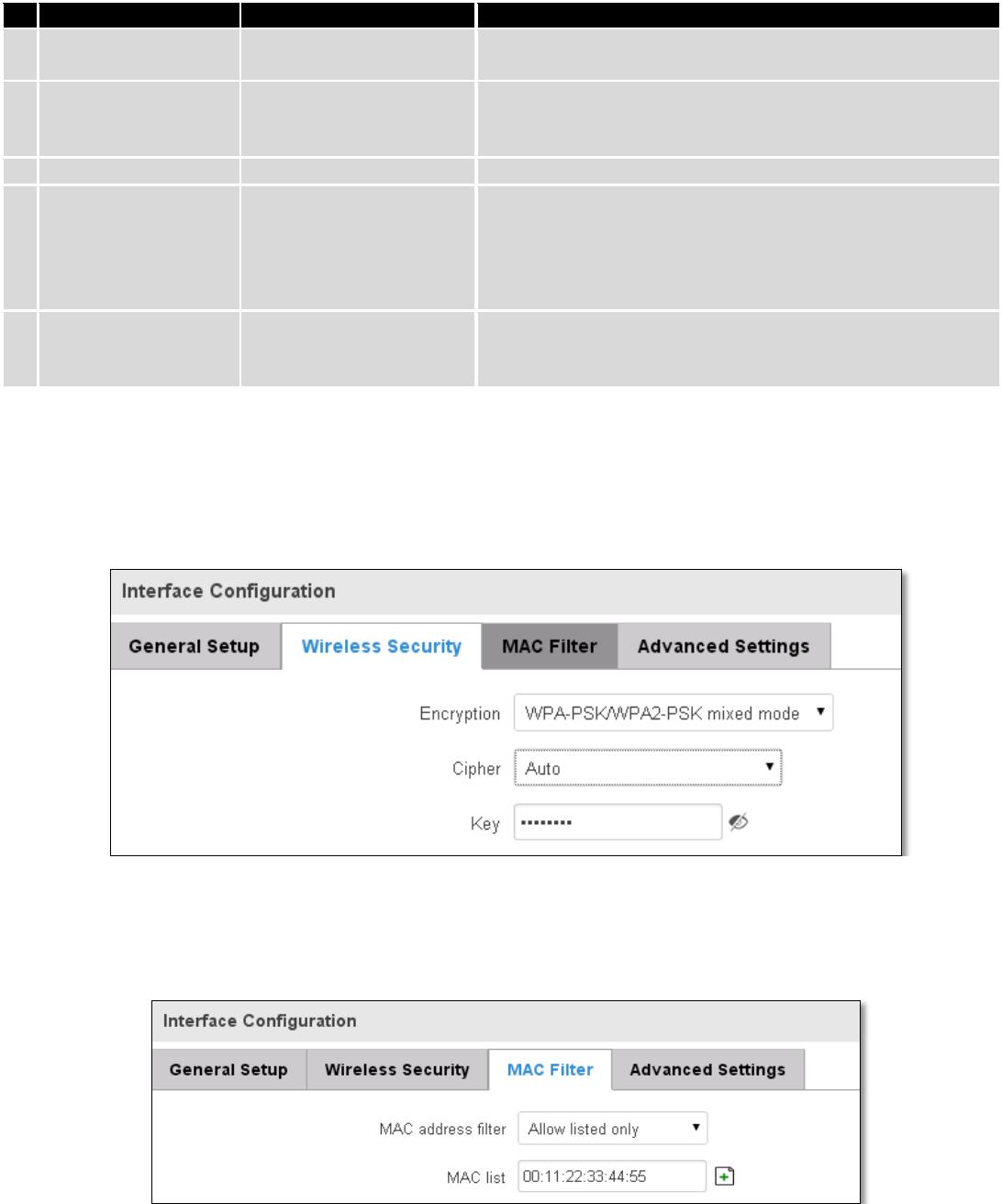
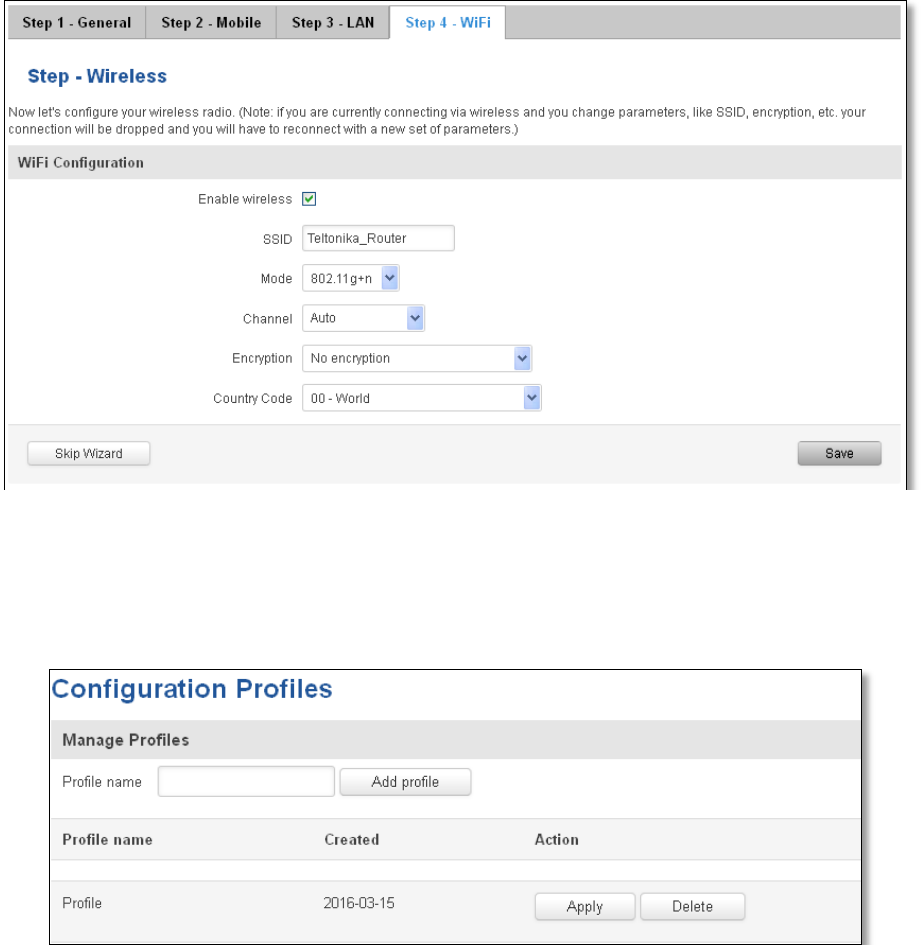
7.4 Wireless ................................................................................................................................................... 64
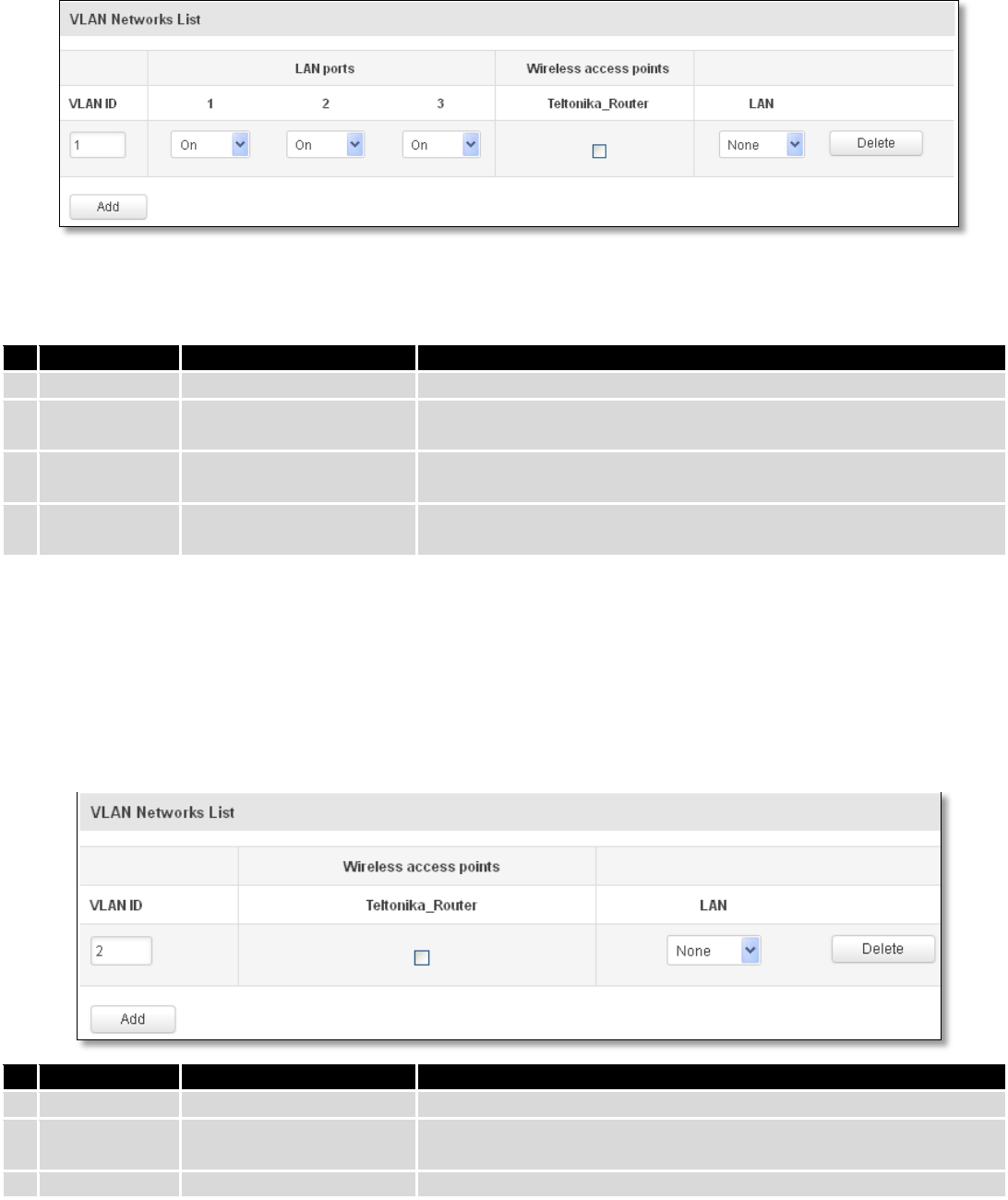
7.5 VLAN......................................................................................................................................................... 67
7.5.1 VLAN Networks ................................................................................................................................ 67
7.5.2 LAN Networks .................................................................................................................................. 69
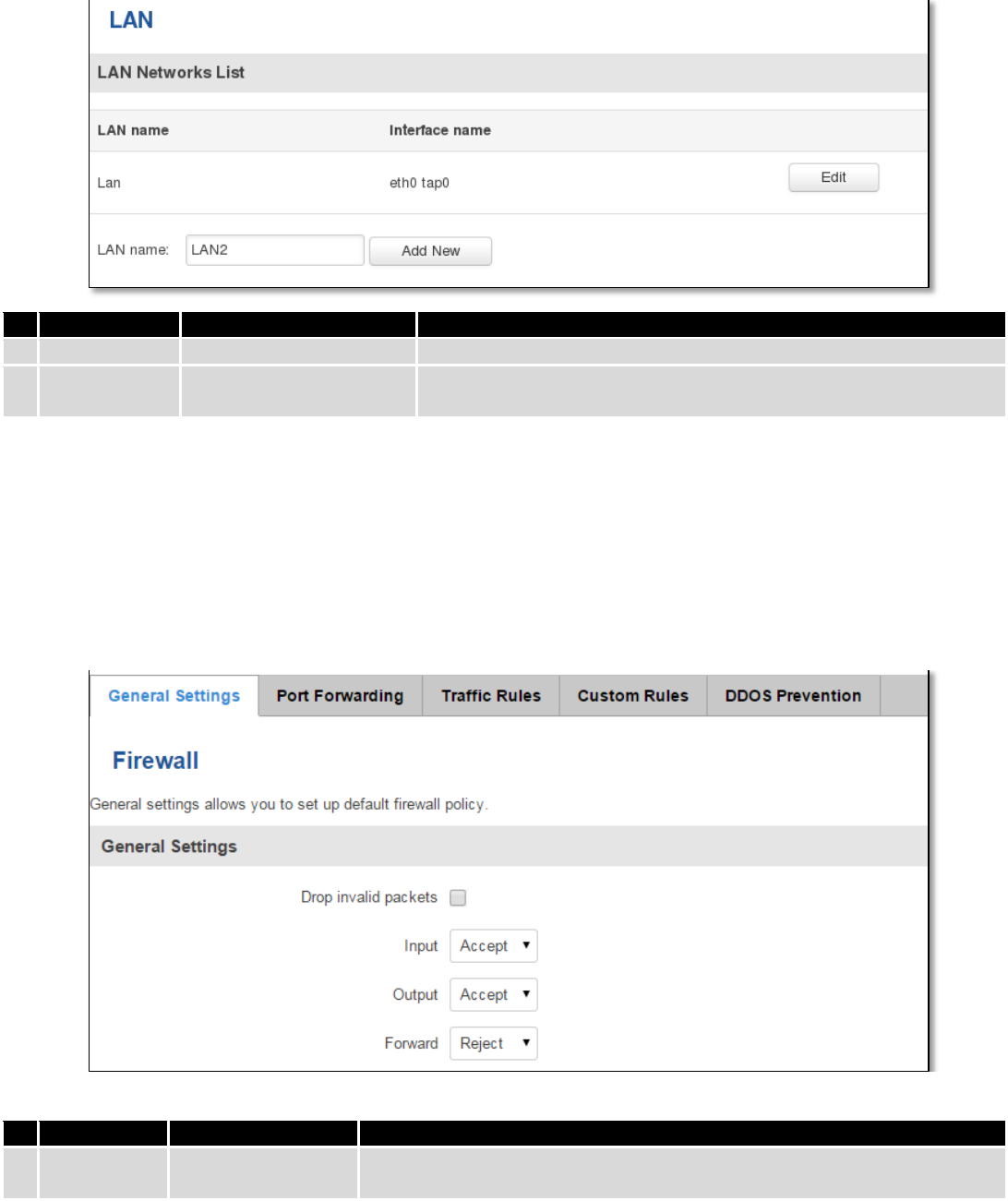
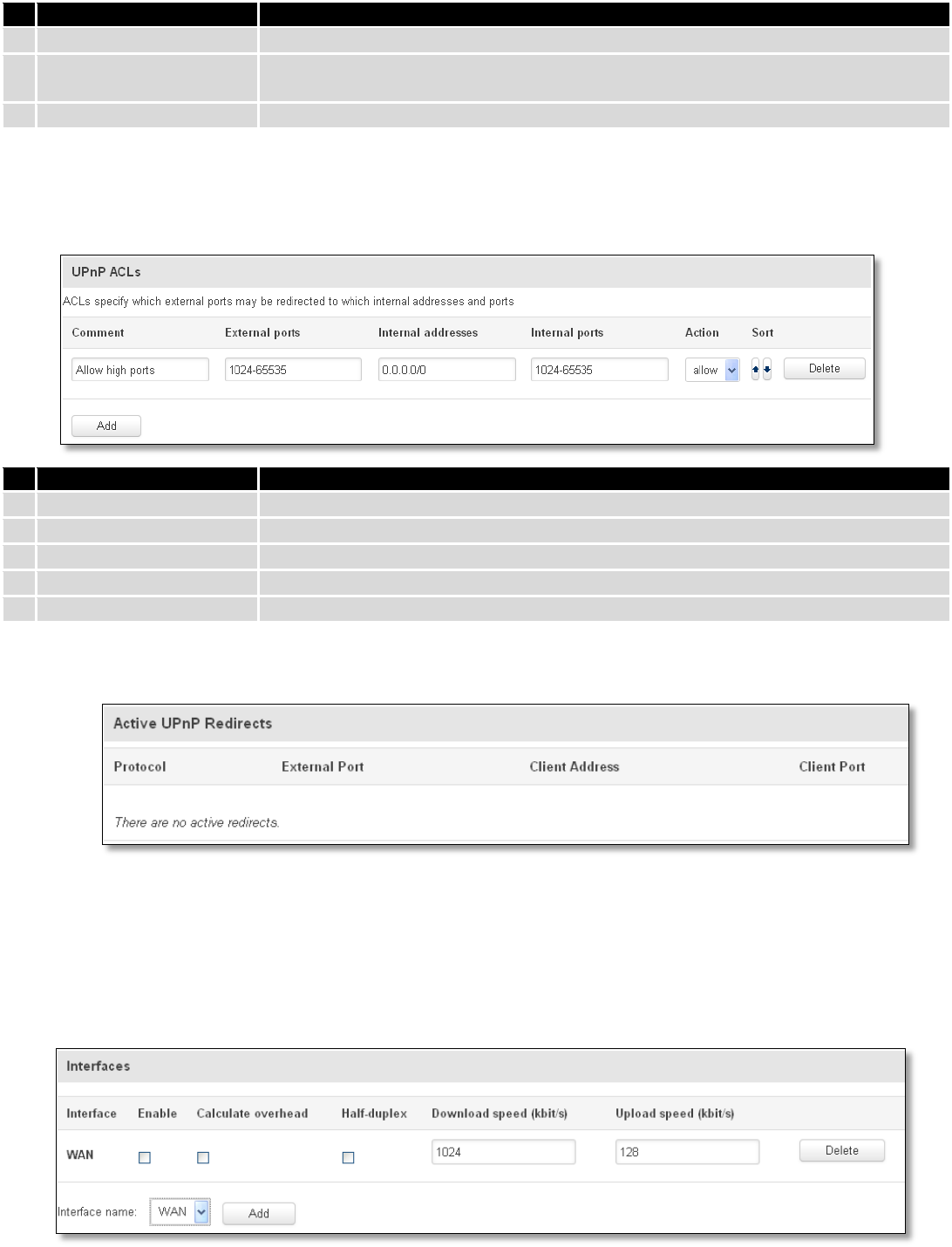
7.6 Firewall ..................................................................................................................................................... 69
7.6.1 General Settings ............................................................................................................................... 69
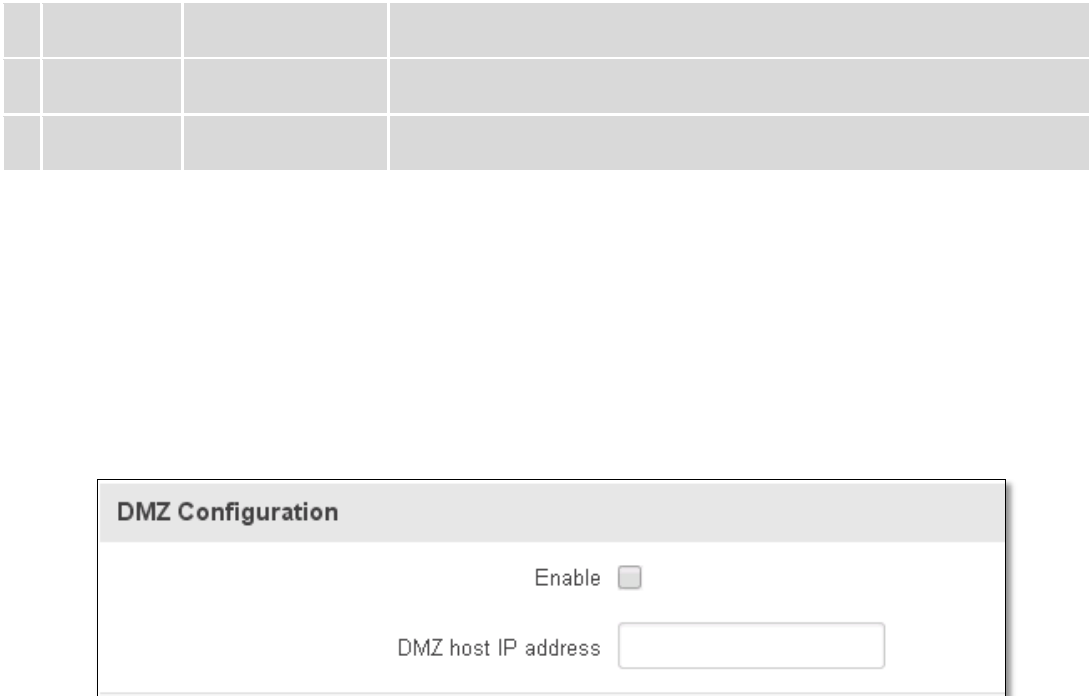
7.6.2 DMZ .................................................................................................................................................. 70
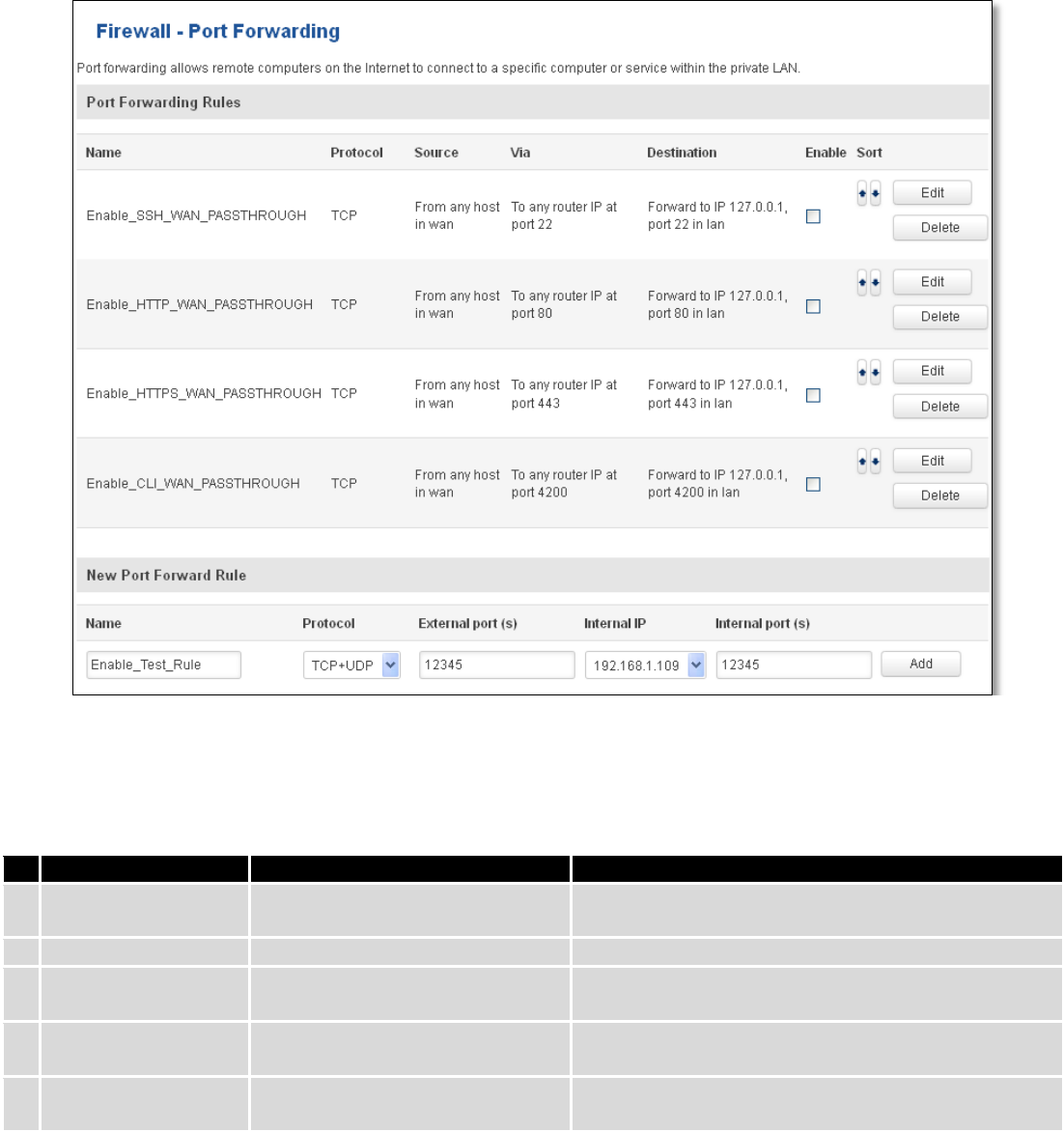
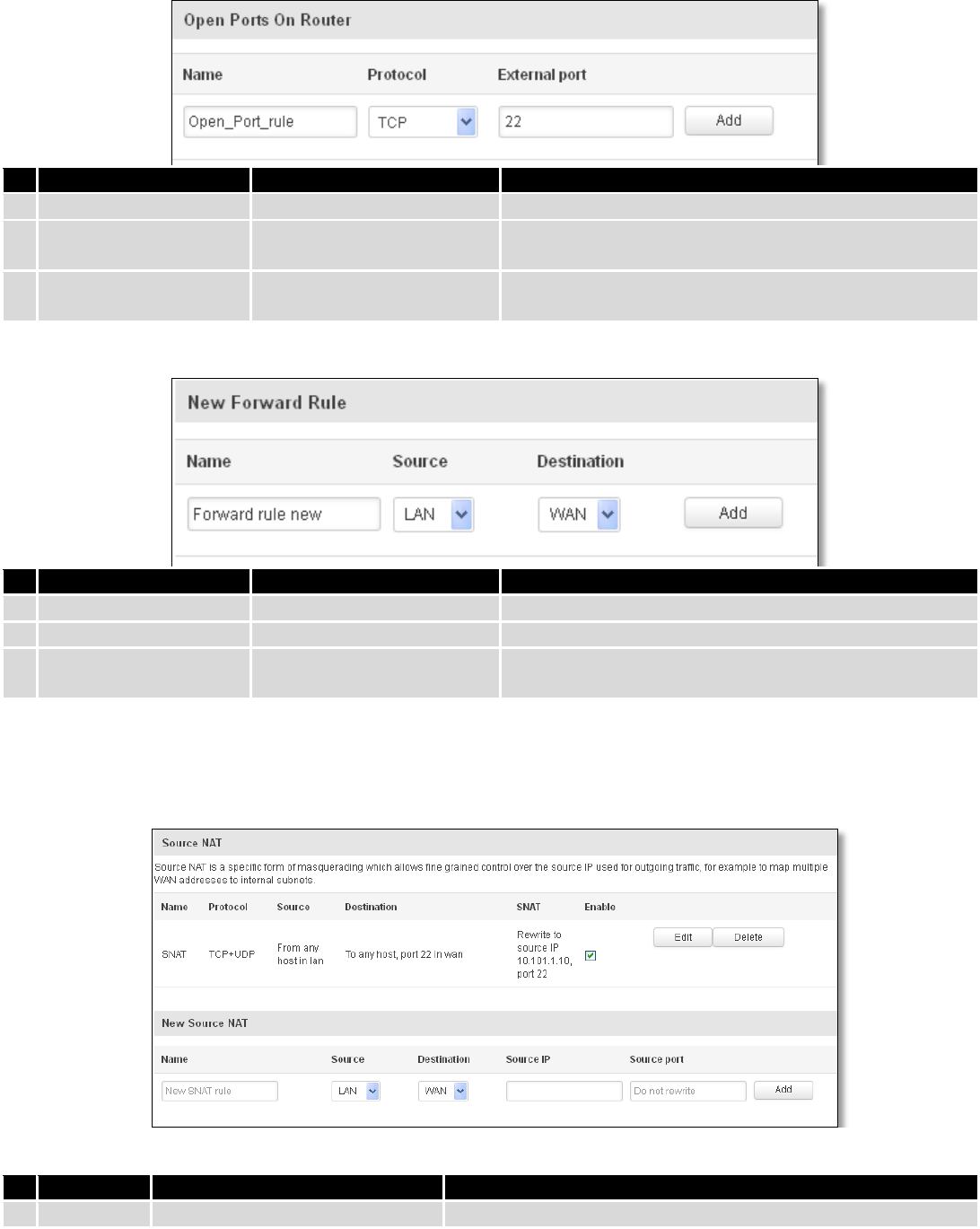
7.6.3 Port Forwarding ............................................................................................................................... 70
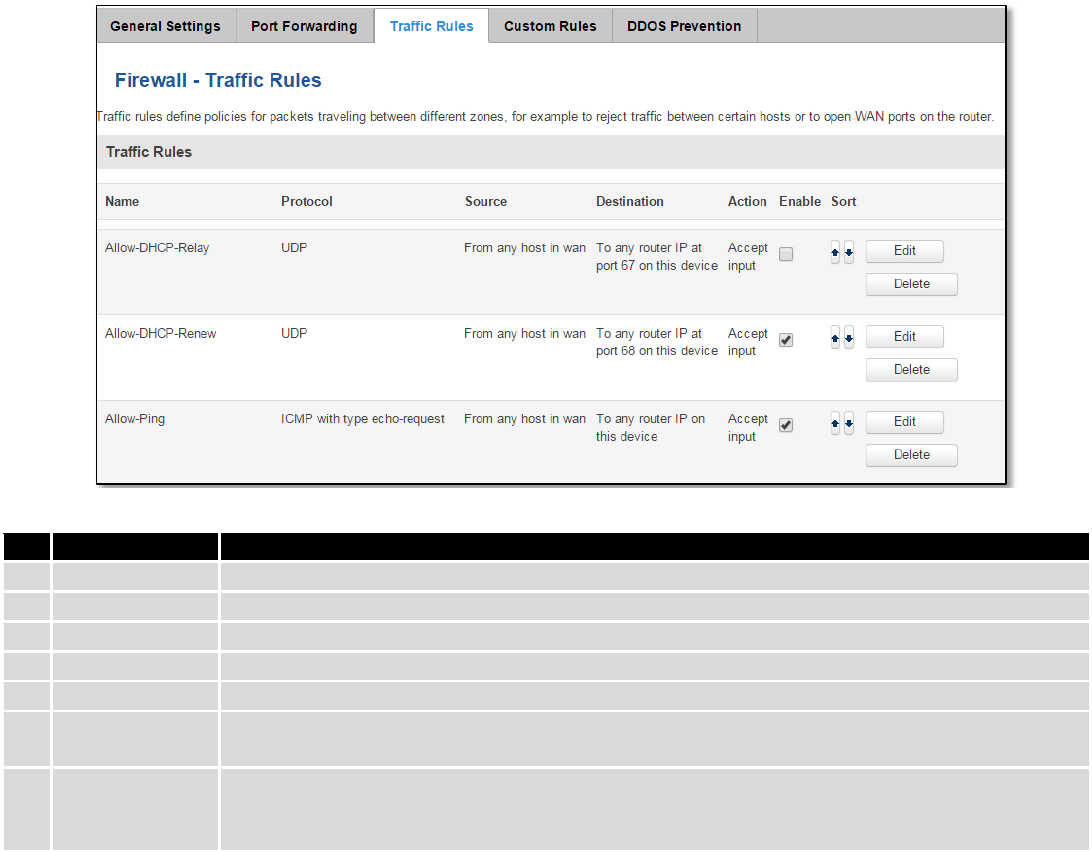
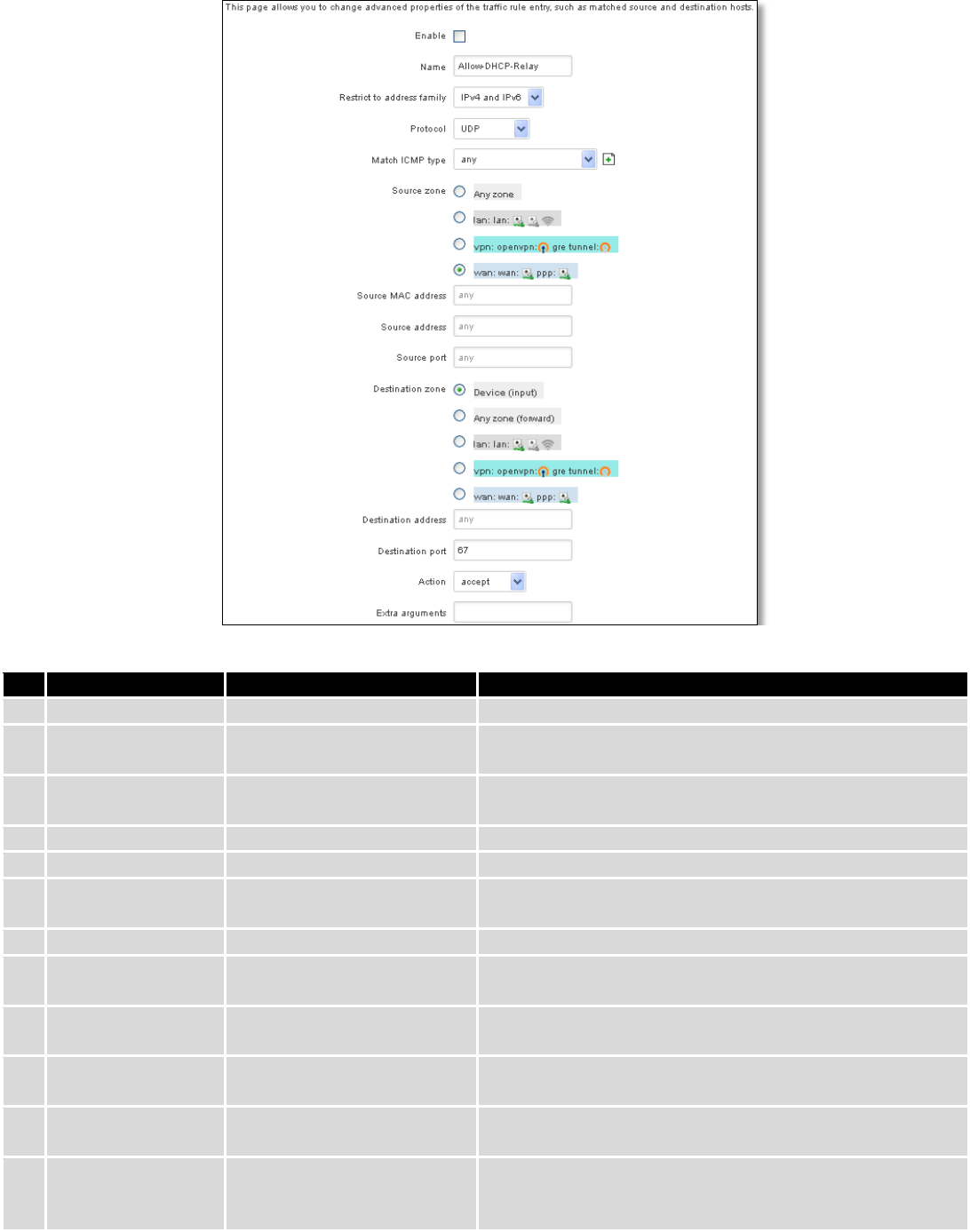
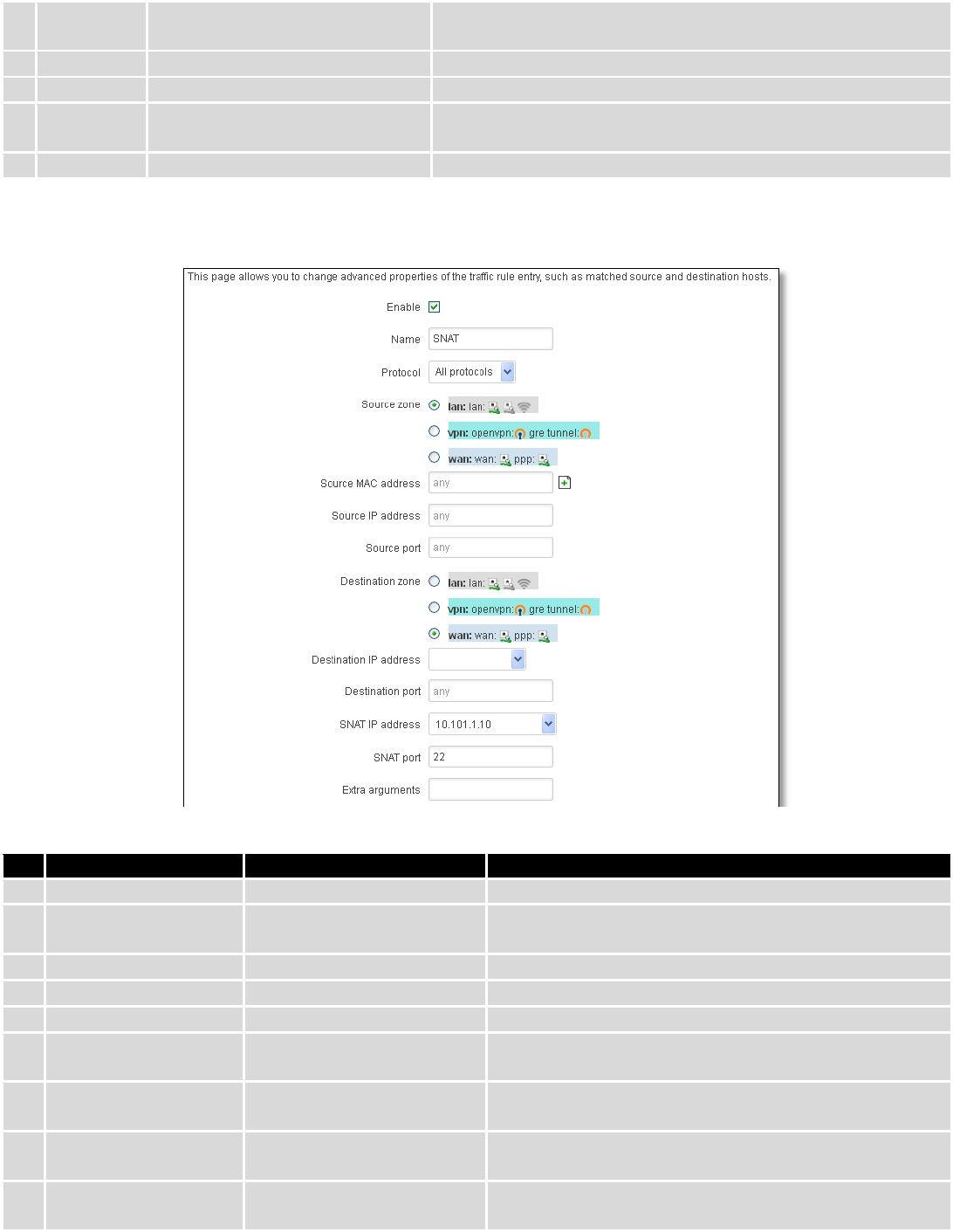
7.6.4 Traffic Rules...................................................................................................................................... 73
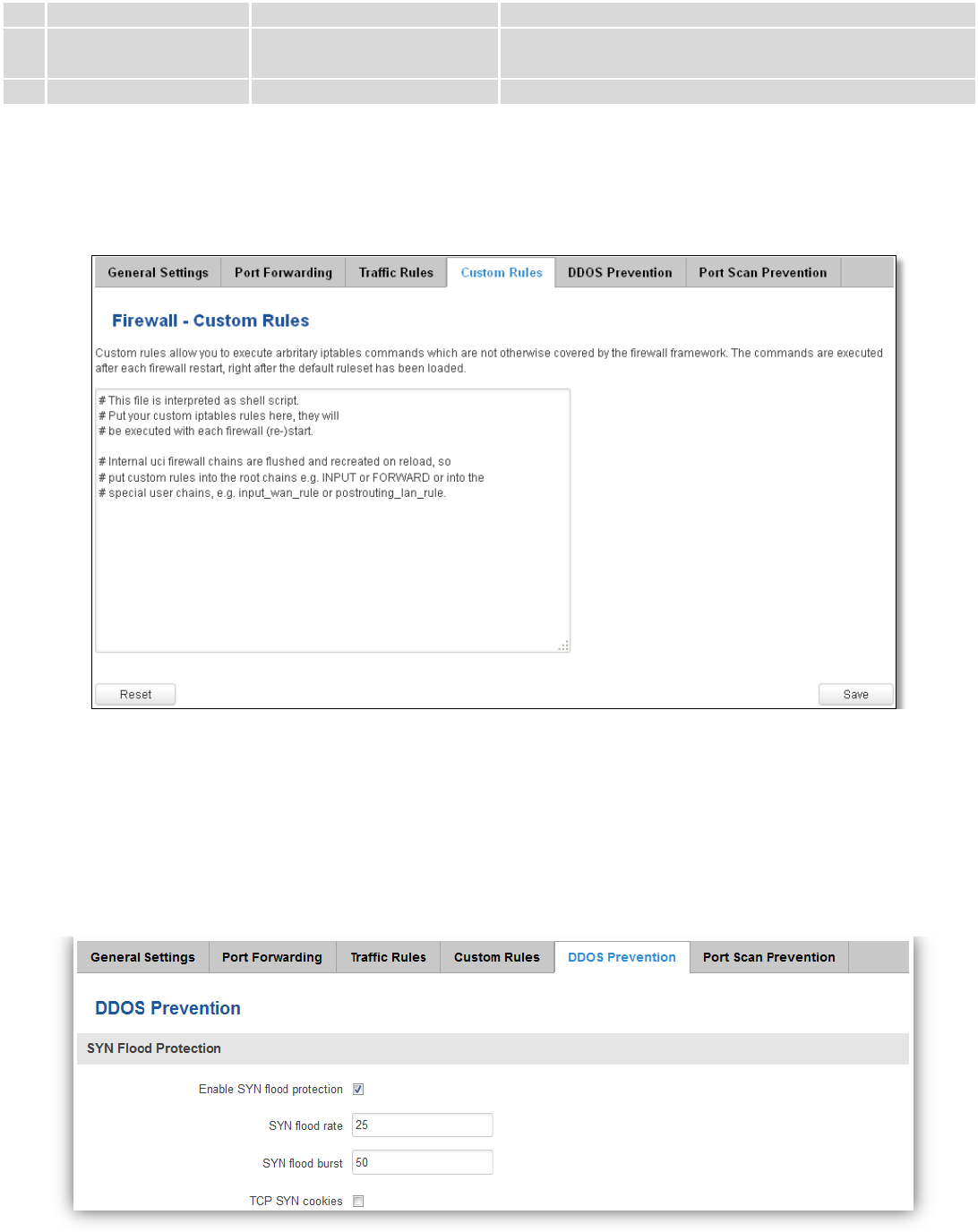
7.6.5 Custom Rules ................................................................................................................................... 77
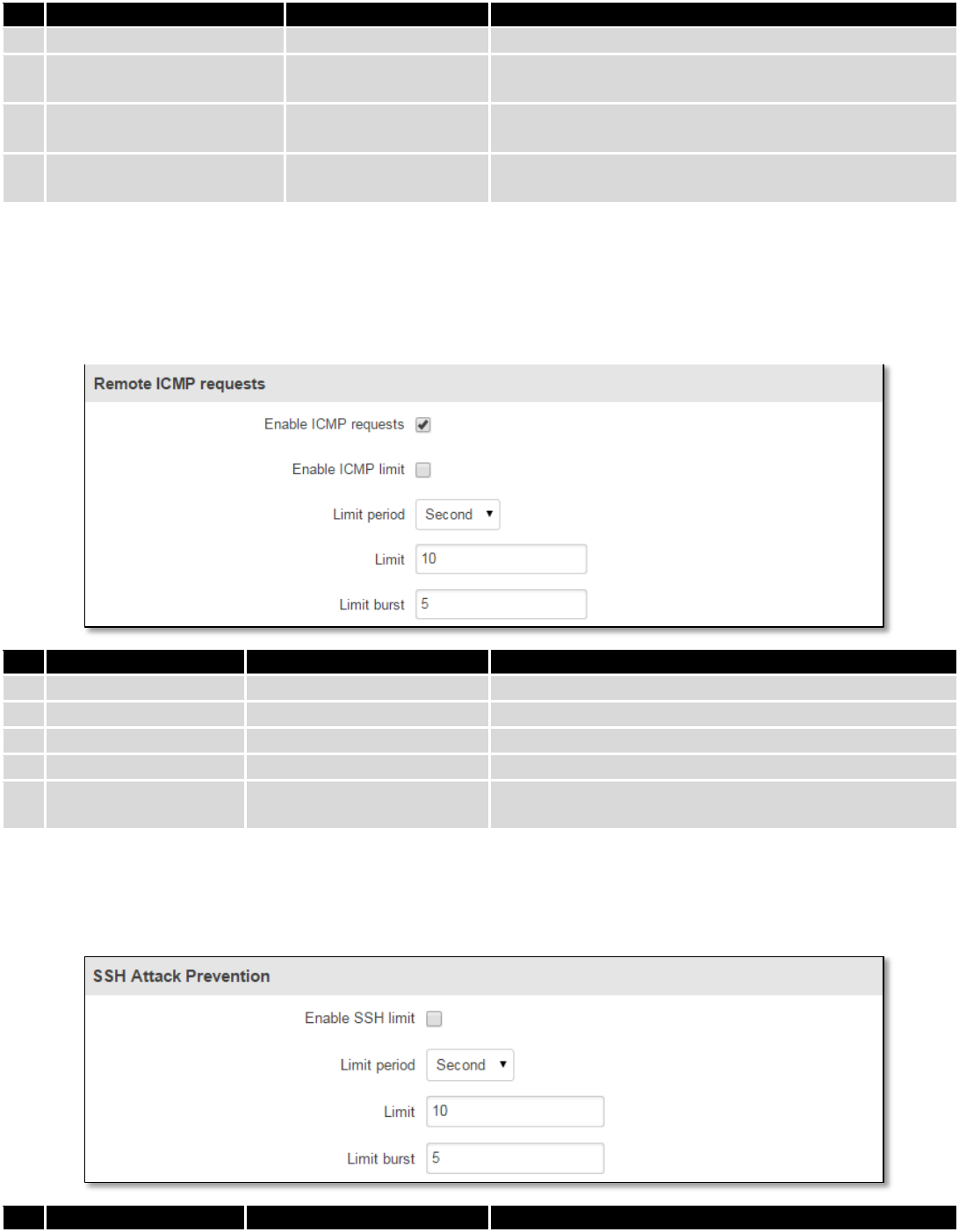
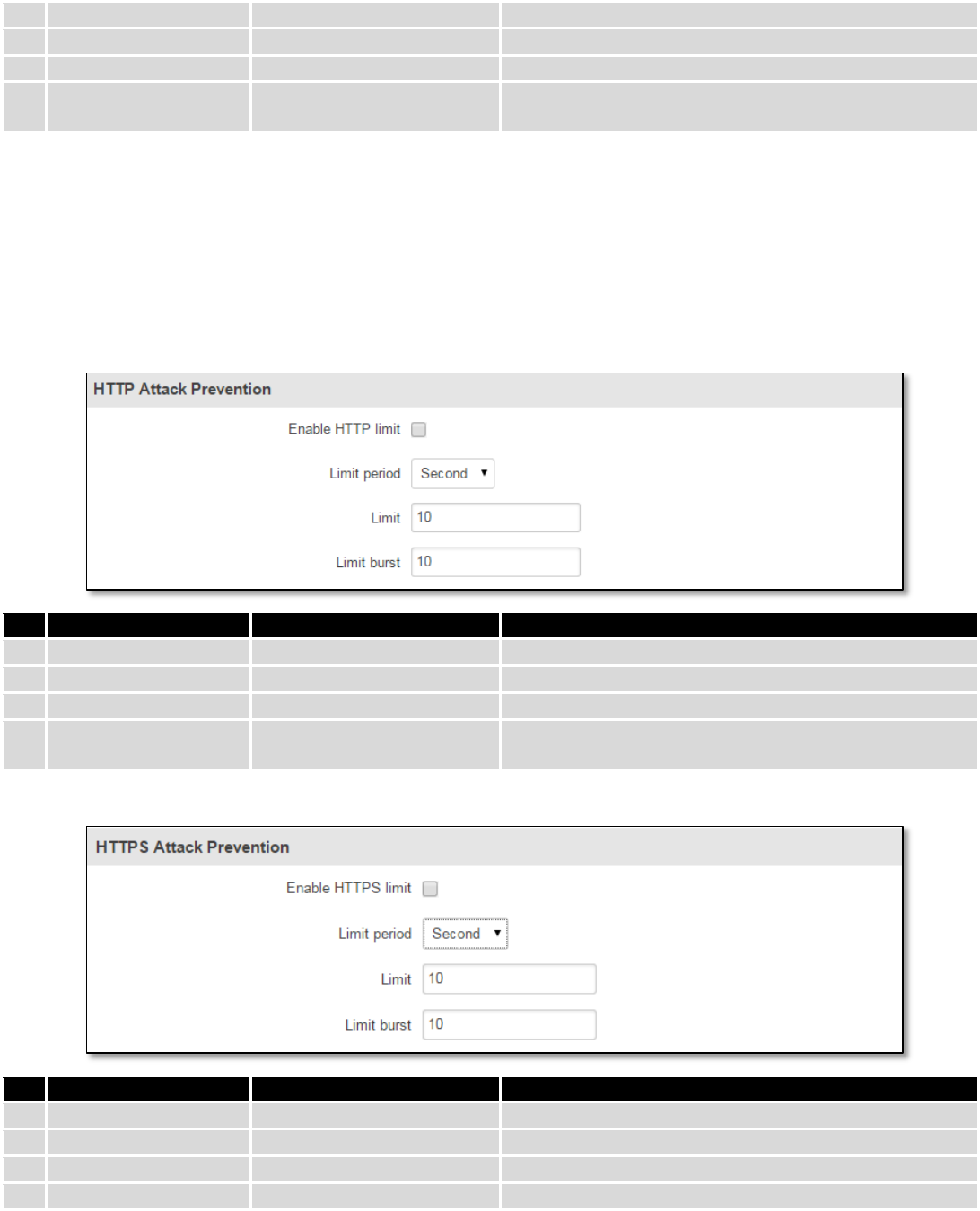
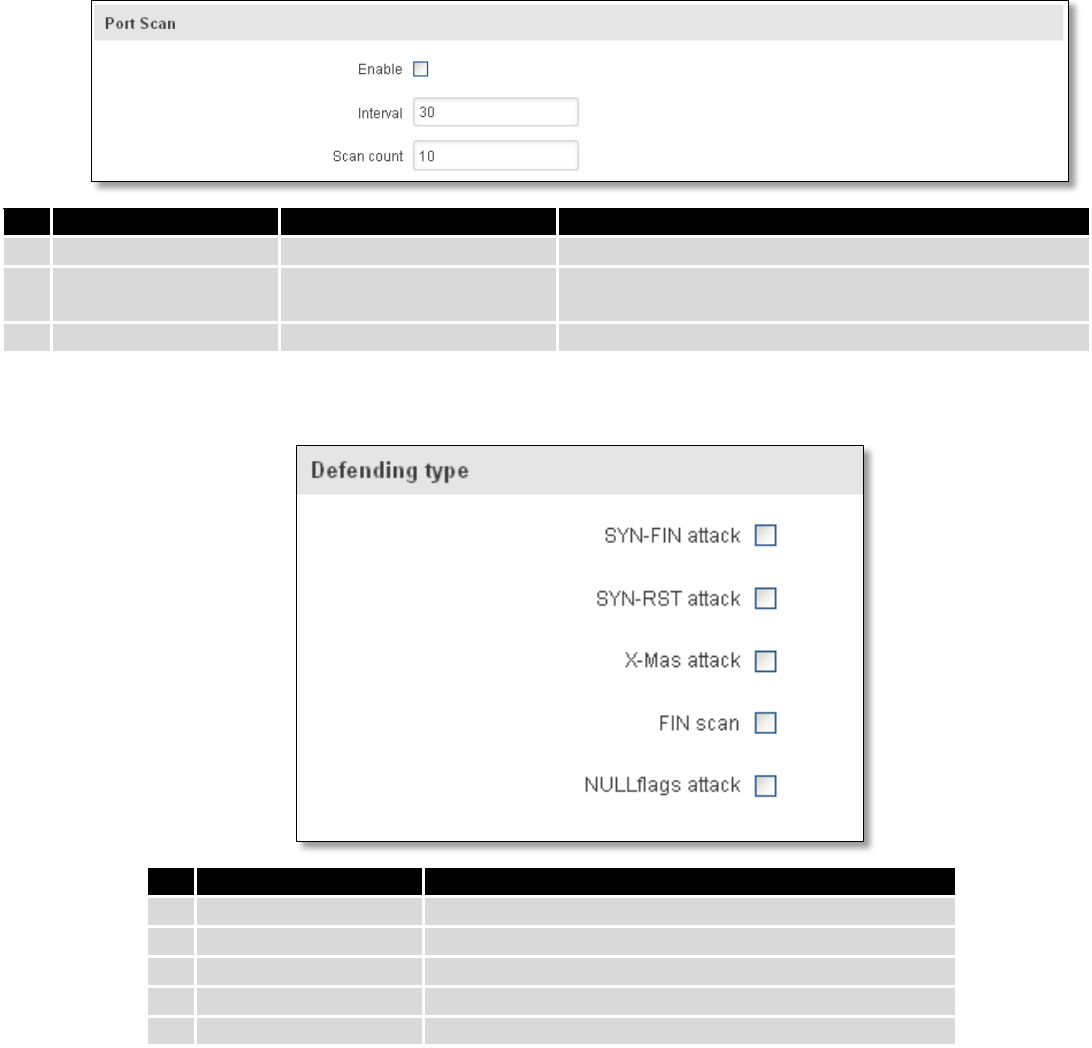
7.6.6 DDOS Prevention ............................................................................................................................. 77